Cisco Duo Single Sign-on SAML Configuration
Overview
This guide will provide you the steps to configure Security Assertion Markup Language (SAML) authentication with Cisco Duo Single Sign-on, providing individual user and group-based identities for policy enforcement.
Prerequisites
Before configuring Cisco Umbrella (End Users) with Duo SSO using Security Assertion Markup Language (SAML) 2.0 authentication you'll first need to enable Duo Single Sign-On for your Duo account and configure a working authentication source.
Deployment
Create the Cisco Umbrella (End Users) Application in Duo
Please note that the following steps come from the Cisco Duo documentation which can be found here. If you have problems with any of the steps, please go to the Duo site to verify the steps and find more information on troubleshooting.
-
Log on to the Duo Admin Panel and navigate to Applications.
-
Click Protect an Application and locate the entry for Cisco Umbrella (End Users) with a protection type of "2FA with SSO hosted by Duo (Single Sign-On)" in the applications list. Click Configure to the far-right to start configuring Cisco Umbrella (End Users). See Protecting Applications for more information about protecting applications in Duo and additional application options. You'll need the information on the Cisco Umbrella (End Users) page under Downloads later.
-
Umbrella uses the Mail attribute, Username attribute, First name attribute, Last name attribute, and Display name attribute when authenticating. We've mapped the bridge attributes to Duo Single Sign-On supported authentication source attributes as follows:
|
Bridge Attribute |
Active Directory |
SAML IdP |
|---|---|---|
| <Email Address> | ||
| <Username> | sAMAccountName | Username |
| <First Name> | givenName | FirstName |
| <Last Name> | sn | LastName |
| <Display Name> | displayName | DisplayName |
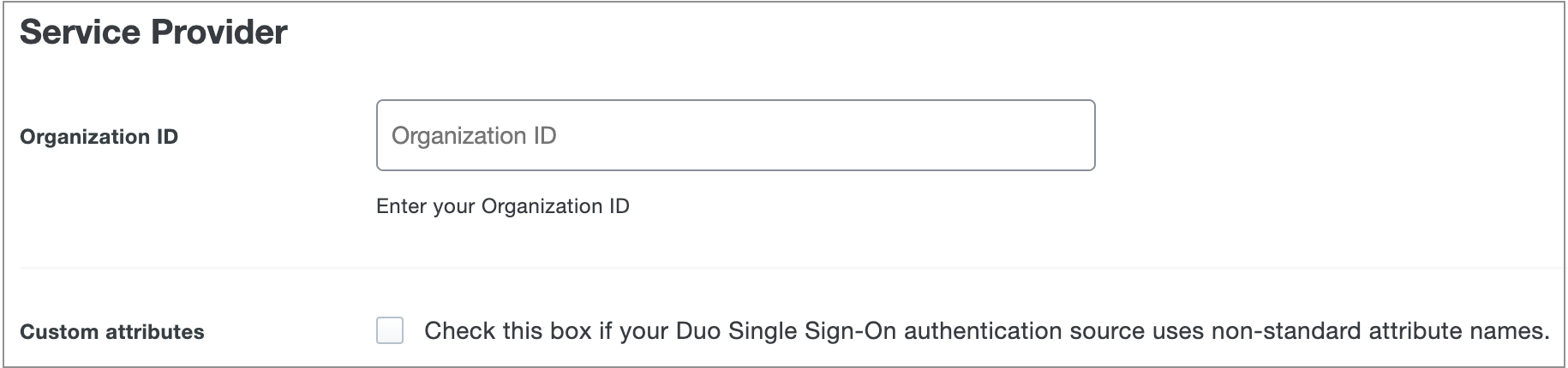
If you are using non-standard attributes for your authentication source, check the Custom attributes box and enter the name of the attributes you wish to use instead.
-
You can adjust additional settings for your new SAML application at this time — like changing the application's name from the default value, enabling self-service, or assigning a group policy.
-
Keep the Duo Admin Panel tab open. You will come back to it later.
Duo Universal Prompt
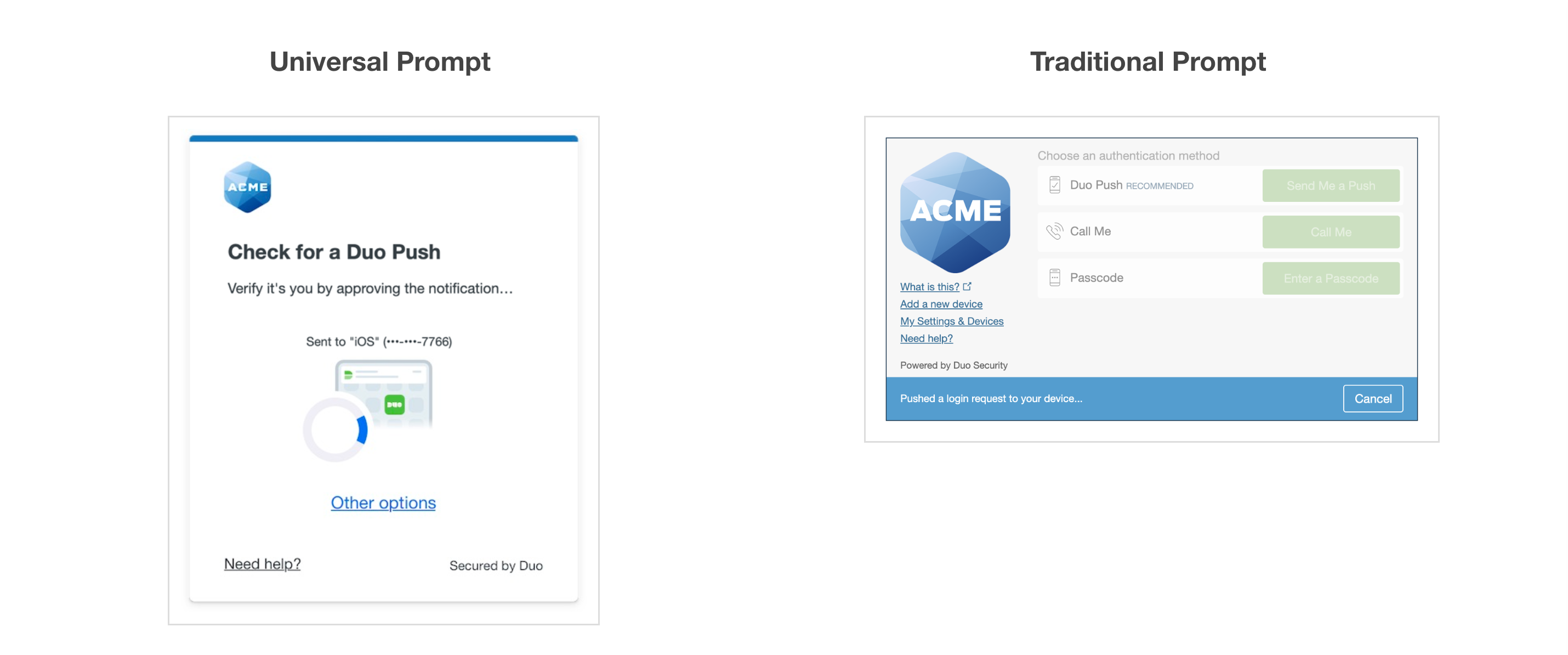
The new Universal Prompt provides a simplified and accessible Duo login experience for web-based applications, offering a redesigned visual interface with security and usability enhancements.
We've already updated the Duo Cisco Umbrella (End Users) application hosted in Duo's service to support the Universal Prompt, so there's no action required on your part to update the application itself. You can activate the Universal Prompt experience for users of new and existing Duo Cisco Umbrella (End Users) applications from the Duo Admin Panel.
Before you activate the Universal Prompt for your application, it's a good idea to read the Universal Prompt Update Guide for more information about the update process and the new login experience for users.
Activate Universal Prompt
Activation of the Universal Prompt is a per-application change. Activating it for one application does not change the login experience for your other Duo applications.
The "Universal Prompt" area of the application details page shows that this application is "New Prompt Ready", with these activation control options:
- Show traditional prompt: (Default) Your users experience Duo's traditional prompt when logging in to this application.
- Show new Universal Prompt: Your users experience the Universal Prompt when logging in to this application.
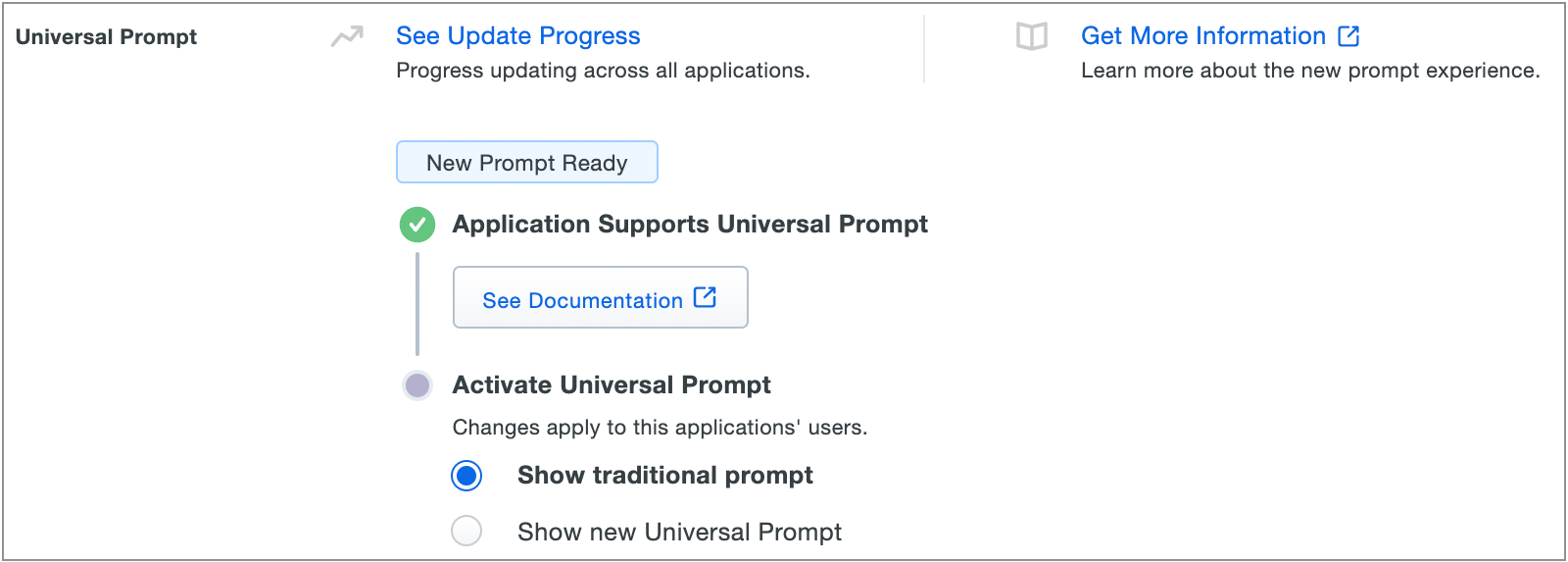
Enable the Universal Prompt experience by selecting Show new Universal Prompt, and then scrolling to the bottom of the page to click Save.
Once you activate the Universal Prompt, the application's Universal Prompt status shows "Update Complete" here and on the Universal Prompt Update Progress report.
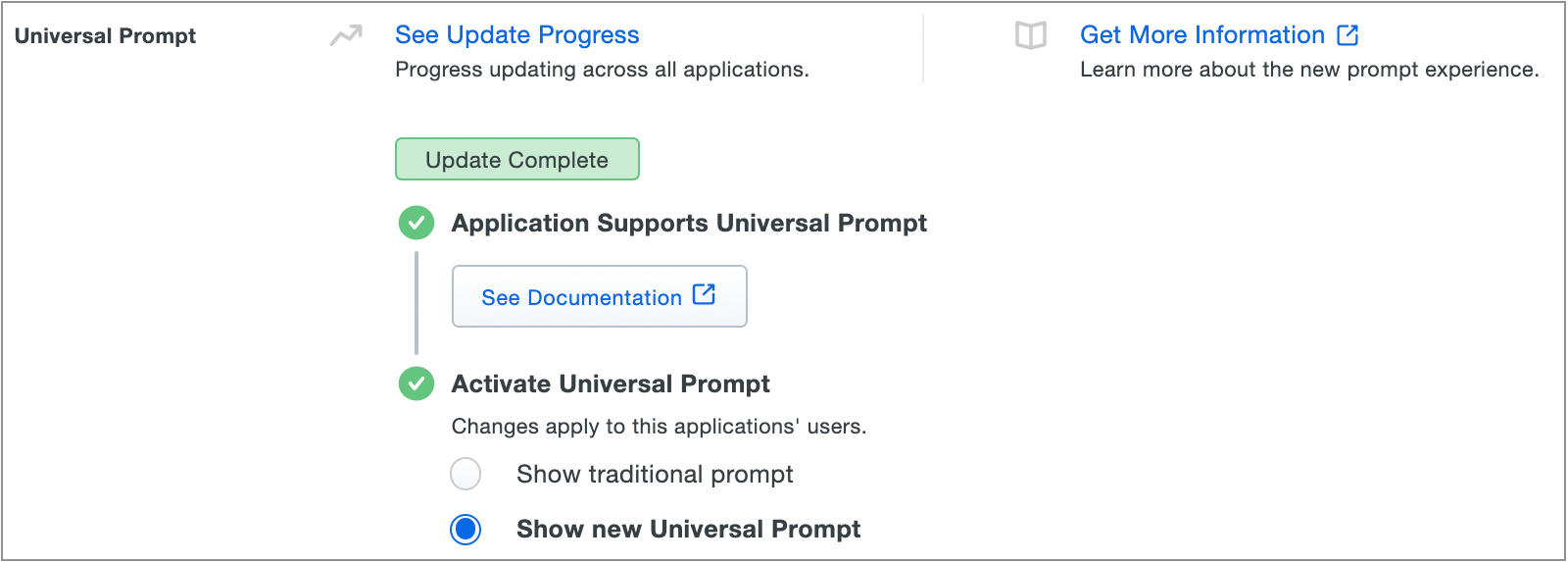
Should you ever want to roll back to the traditional prompt, you can return to this setting and change it back to Show traditional prompt.
Universal Update Progress
Click the See Update Progress link to view the Universal Prompt Update Progress report. This report shows the update availability and migration progress for all your Duo applications in-scope for Universal Prompt support. You can also activate the new prompt experience for multiple supported applications from the report page instead of visiting the individual details pages for each application.
Enable Duo Single Sign-On
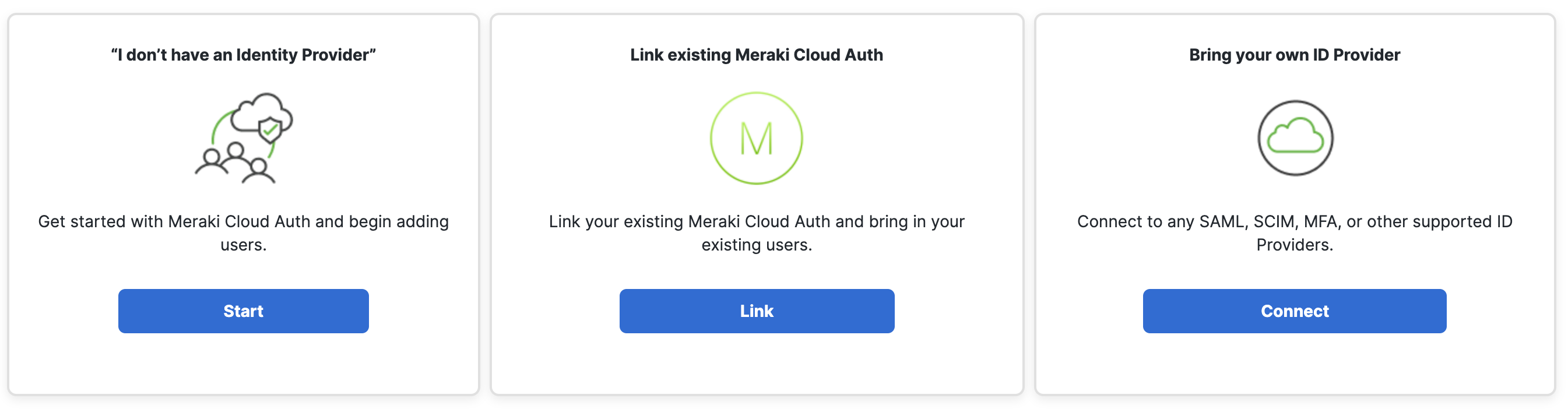
- Open a new tab and log into the Secure Connect dashboard. Go to Secure Connect -> Identities & Connections -> Users, select your identity provider, click Connect under "Bring Your own ID Provider".
- Click Configure SAML.
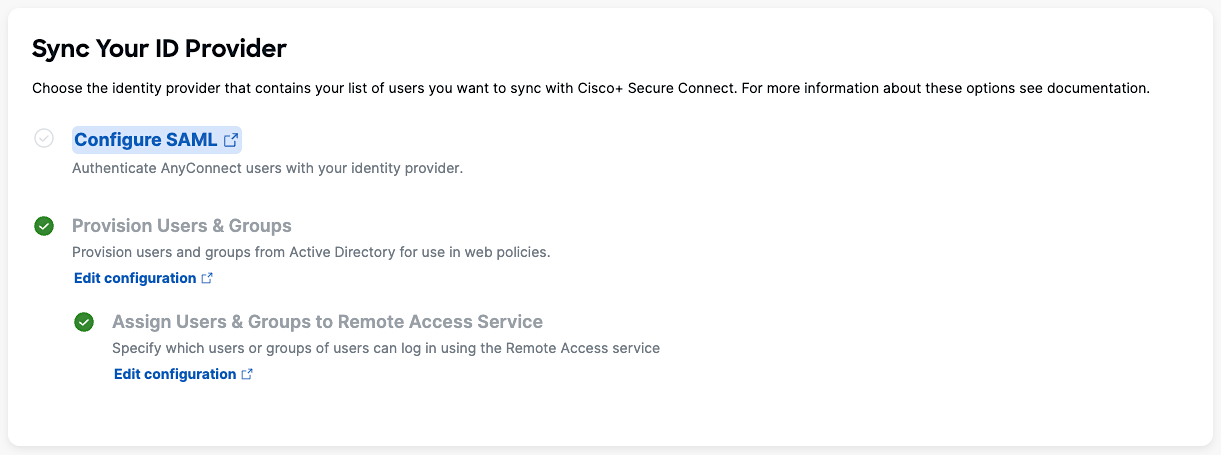
- This will take you to the Cisco Umbrella Dashboard. You should on the Deployments -> Configuration -> SAML Configuration page. From here, click the Add button on the top right corner.
- Select Duo Security as your Identity Provider (IdP).
- Turn on Organization-specific Entity ID Enabled to enable the entity if you have multiple Secure Connect Orgs and need to configure SAML authentication for these Orgs against the same IdP. Otherwise, leave it uncheck by default and click Next.

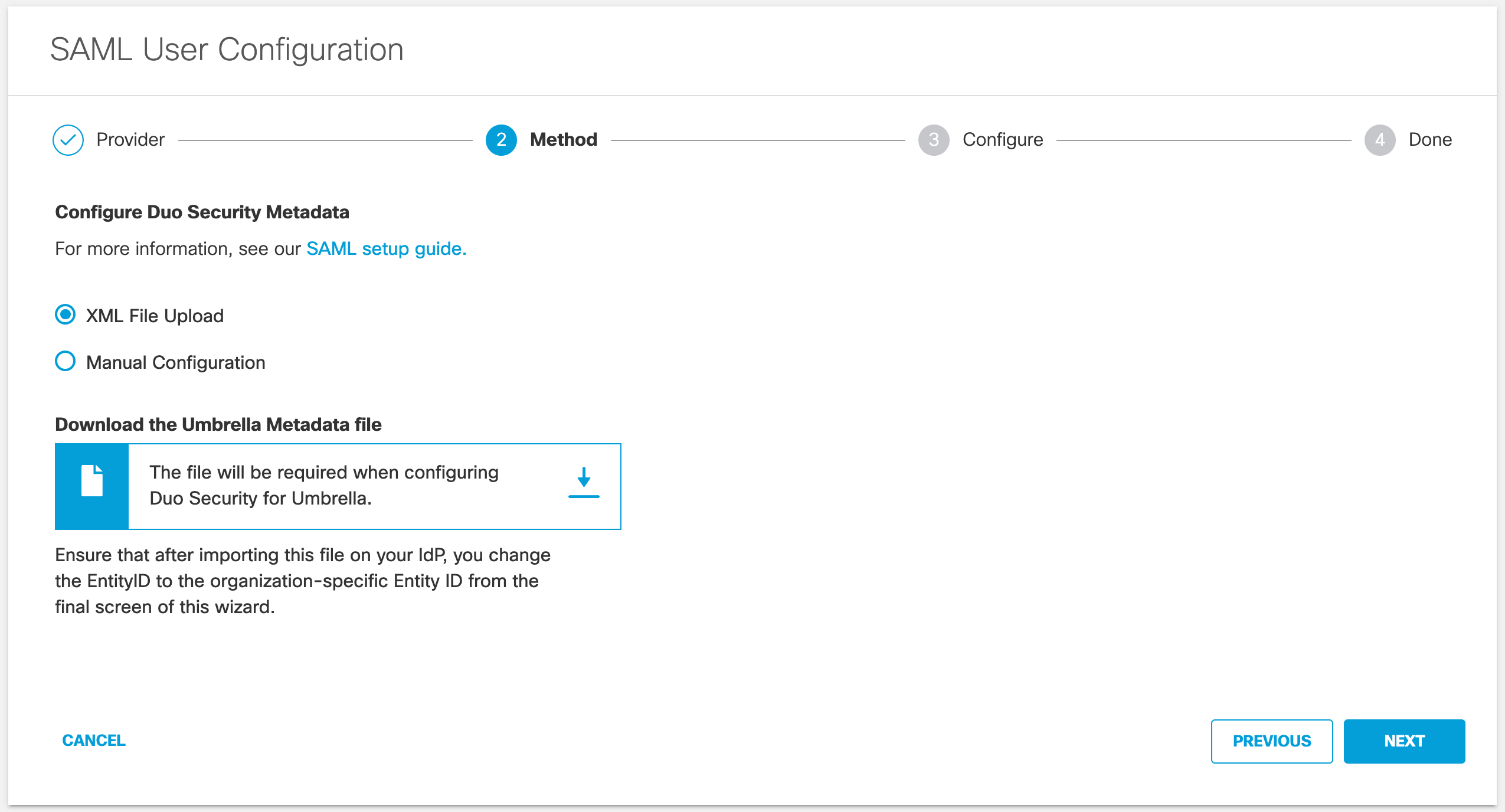
-
Make sure XML File Upload is selected and click Next.
-
Return to the Duo Admin Panel. Go to Applications, click Protect an Application on the top right corner and search for Cisco Umbrella (End Users). Then click Protect.


-
Enter your Umbrella Organization ID under the Service Provider section. Then scroll down and click Save.
(Notice: The Umbrella Orgnization ID is numbers that can be find in the url, for example, 8235***)


-
Under Downloads section, click Download XML button next to the "Identity Provider XML Metadata" to download the Duo Single Sign-On IDP Metadata XML file.

-
Return to your Umbrella dashboard and upload the Duo Security Metadata XML file and click Next.

11. From the Re-Authenticate Users drop-down list, choose how often Umbrella re-authenticates users: Never, Daily, Weekly, or Monthly.

12. Click Save. Your new configuration appears as SAML Web Proxy Configuration.

13. To quick validate your configuration. Click TEST CONFIGURATION on the "SAML User Configuration" page and follow the on-screen prompts to log in with Duo.


