Mitigating a Spoofed AP with Air Marshal
Learn more with these free online training courses on the Meraki Learning Hub:
Spoof detection in Dashboard
A node will indicate a spoof if it detects another radio broadcasting the same SSID outside the organization.
When a spoof is seen, it will appear in Wireless > Monitor > Air Marshal on the Dashboard.
- Determine which of the Access Points is being spoofed. The affected AP's MAC address can be seen under the Spoof section.

List of spoofs will be updated on an hourly interval.
Spoofs cannot be contained or mitigated the same way a rogue or other SSID because you would be containing the Meraki network SSID as well. The only way to deal with a spoof is through a "Boots on the ground" approach.
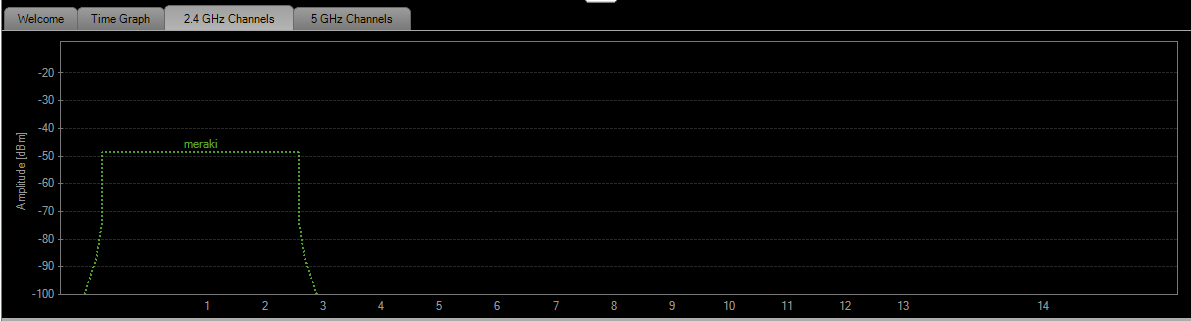
2. Disable the particular AP being spoofed. Then, using a WI-FI scanner (such as inSSIDer) measure the signal strength of the SSID and determine where it is strongest. This will require taking various strength measurements from multiple locations. This process will give a good idea of where the Spoofing device is located so appropriate actions can be taken to disconnect the device.