Storm Control
Click 日本語 for Japanese
Basic Storm Control
Storm control on MS series switches protects LAN connectivity in the event of a packet storm in a network. All MS series switches include control plane policing of STP and CDP/LLDP floods to ensure Meraki Cloud connectivity.
Enhanced Storm Control
Note: The Storm control settings will only be visible if the network contains a supported switch model. This is also applies to Templates and bound Switch profiles. A supported switch must be bound to a profile in order for the Storm control settings to become visible.
Enhanced Storm Control can be enabled on supported switches to suppress Broadcast, Multicast and Unknown Unicast packets based on a percentage of traffic on a given interface. Suppression monitors the bandwidth of each individual switch port every 1 second. On classic MS switches, if the specified type of traffic exceeds the defined limit, only excess packets will be dropped. On Catalyst switches, if the specified type of traffic exceeds the defined limit, all packets will be dropped until the monitored traffic falls below the defined limit.
Supported Models
Supported models: MS100 series, MS210, MS225, MS250, MS350, MS355, MS400 series, and Catalyst switches.
Enabling Enhanced Storm Control Globally
To enable Enhanced Storm Control globally:
1. Navigate to Switch > Configure > Switch Settings
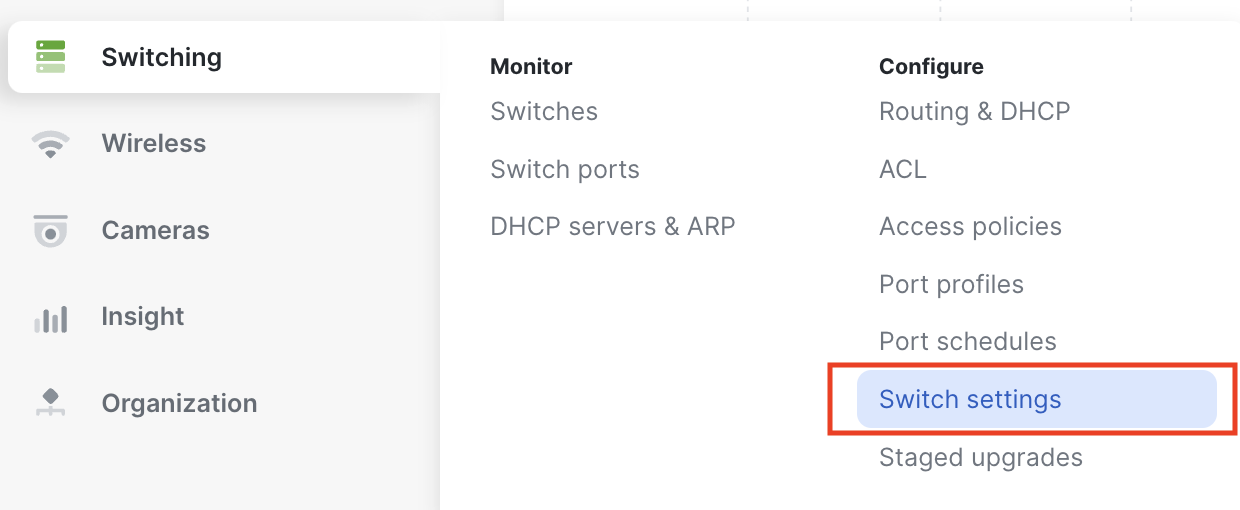
2. In the Storm Control section, select Add a storm control rule
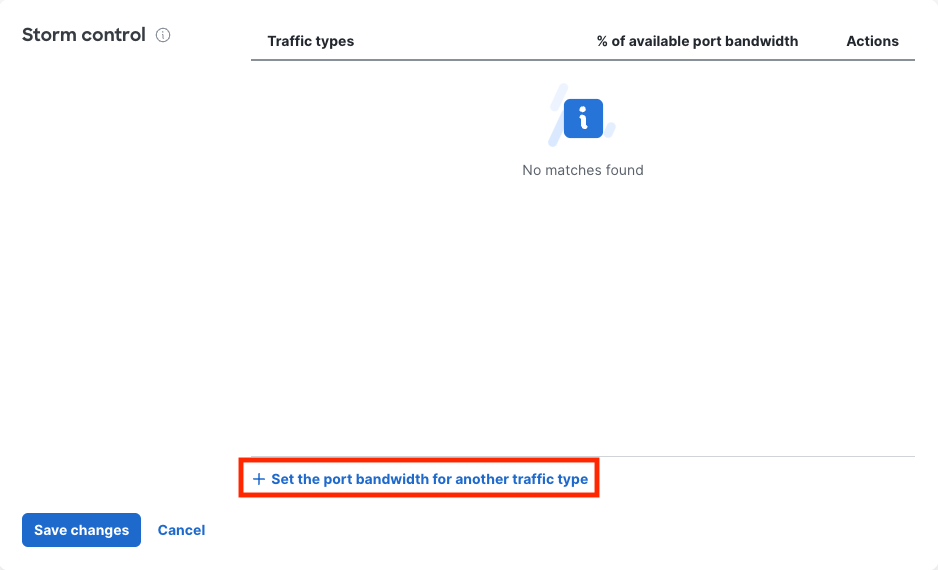
3. From the Traffic Types drop down, select the type of traffic you wish to suppress (Broadcast, Multicast, and/or Unknown Unicast)

4. In the % of available port bandwidth field, enter a percentage between 1 - 99% to complete the configuration of the rule

5. Click Confirm

6. Select Save at the bottom of the settings page to save your configurations

Configuring Port Level Enhanced Storm Control
Note: Port level control is only available if Enhanced Storm Control is enabled globally. Once Enhanced Storm Control is enabled globally, it is enabled on each port by default.
To configure Enhanced Storm Control at the port level:
1. Navigate to Switch > Monitor > Switch ports
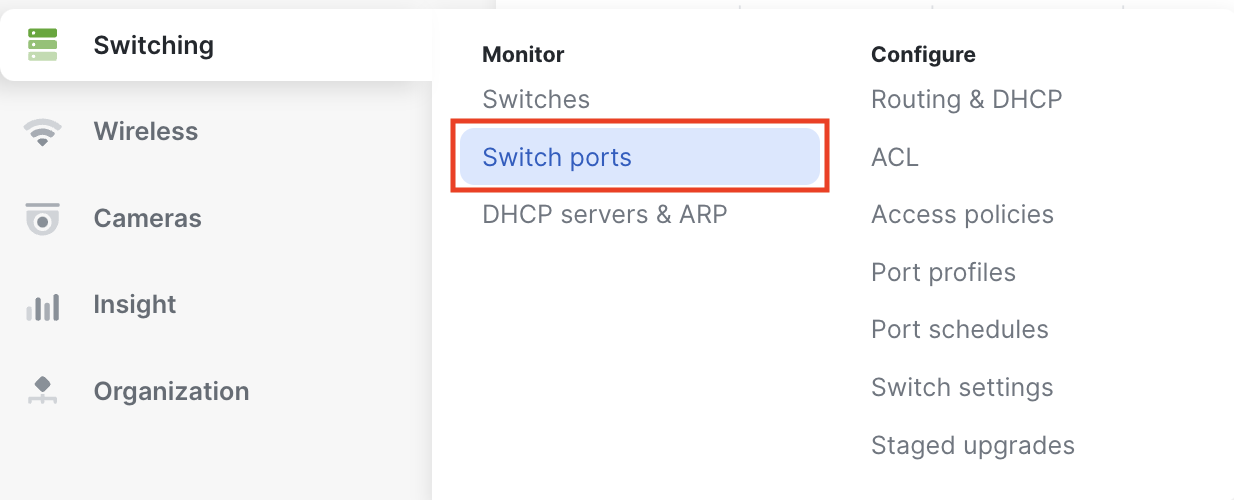
2. Select the switch port to configure
3. In the Storm Control section, select Enable or Disable

4. Select Update to save the port configuration

Platform Behavior Considerations for IOS XE switches
Storm Control Behavior May Vary by Hardware Platform
Storm control limits broadcast, unknown unicast, and multicast traffic at the port level. However, how multicast traffic is classified and limited can vary depending on the underlying switch hardware platform.
Multicast Traffic Handling
On all platforms, storm control applies to multicast traffic based on traffic thresholds. However:
- Some platforms treat all multicast traffic equally
- Others can distinguish between control-plane traffic (such as routing protocols) and data-plane multicast
In practice, this means that on certain switch models, including older models, storm control:
- Applies to all multicast traffic
- May impact:
- Routing protocols (e.g., OSPF)
- Multicast control traffic (e.g., IGMP, PIM)
In these cases, enabling multicast storm control at low thresholds may disrupt network control protocols
On newer hardware platforms:
- Storm control is applied more selectively
- Control-plane traffic (such as routing protocols) is typically not impacted
- Storm control primarily limits:
- Flooded or excessive multicast data traffic
This allows storm control to be used more safely in environments with dynamic routing or multicast applications
Important Considerations
- Storm control behavior is hardware-dependent, even when configured through the same dashboard
- Behavior may also vary with:
- Firmware version
- Feature interactions (QoS, multicast configuration, etc.)
Best Practices
- Avoid setting multicast storm control thresholds too low in networks using:
- Dynamic routing (e.g., OSPF)
- Multicast applications
- Validate behavior in your environment, especially when using:
- Mixed hardware platforms
- Cloud-managed Catalyst switches
- Consider using additional protections such as:
- Multicast configuration (e.g., IGMP snooping)
Note: For detailed platform-specific behavior, refer to Cisco Catalyst documentation for your switch version/model.
| Platform | IOS XE 17.15.x | IOS XE 17.18.x | IOS XE 26.1.x |
| Catalyst 9200 | Link | Link | Link |
| Catalyst 9300 | Link | Link | Link |
| Catalyst 9350 | N/A | Link | |
| Catalyst 9500 | Link | Link | Link |
| Catalyst 9600 | Link | Link | Link |
| IE-3500 | N/A | N/A | Link |

