NAT Detection on MS Switches
Requirements
NAT detection is supported on the following platforms and firmware versions:
| MS Switch Family | MS Switch Model | Minimum Firmware Required |
| MS210 | MS 14 | |
| MS200 Series | MS225 | MS 14 |
| MS250 | MS 14 | |
| MS 300 Series | MS355 | MS 14 |
| MS410 | MS 14 | |
| MS400 Series | MS425 | MS 14 |
| MS450 | MS 14 |
Details
MS switches can alert an administrator if a device is detected that appears to be using Network Address Translation (NAT). NAT on the LAN may indicate the use of a rogue AP or router, but also may be used for legitimate purposes with technologies such as containers, or tracking prevention.
NAT detection compares observed traffic patterns to various signatures that may indicate multiple separate hosts are communicating through a single IP address. For example, TCP timestamps that that indicate multiple clocks, or source ports that appear across multiple ranges could indicate more than one device is using a particular address.
Modern operating systems use a number of tracking prevention methods that can resemble the behaviour of many hosts behind a single NAT IP. Therefore NAT detection may also cause alerts for legitimate traffic that may not be related to NAT.
It is recommended to tune the alert frequency to a suitable value for your network, then investigate to determine whether further action should be taken.
Configuration
To enable NAT detection on MS switches, log into the Meraki dashboard for a network that contains MS switches and navigate to Network-wide > Configure > Alerts.
In the "Switch" section, click the check box for the "A client is detected sharing its IP address via NAT." option:
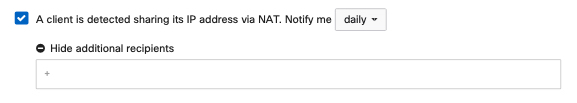
Select to be alerted ASAP, daily, or weekly, and optionally define additional alert recipients. Daily or weekly alerts may be appropriate if you find that a large amounts of alerts are generated frequently using the ASAP option.
Alert Example
Alerts appear somewhat different between email or webhooks, but contain similar information in both cases. The alert will indicate the client IP address that might be being used by multiple hosts, the last time an indication of NAT was detected, a suspected number of real hosts sharing that IP address, and the number of switches detecting the behaviour:


