Network Objects Configuration Guide
Click 日本語 for Japanese
Overview
Network Objects is one of the supported categories of Policy Objects. In the future, we will introduce additional categories such as Application, Ports and etc.
Network Objects provide easier management of firewall rules. They serve as labels to IP Subnets and FQDN that can be used on access policies such as firewall rules. If there are needs to modify multiple access policies that use the same IP Subnets or FQDN, you only need to modify the Network Object to have it reflect on all policies.
For additional highlights of the feature, please see Network Objects Highlights.
Learn more with these free online training courses on the Meraki Learning Hub:
Use Case
Network Objects are ideal for networks that have large and complex firewall rules. This feature simplifies management of firewall rules and allows rules to be easily identified.
Feature
Network Objects can be centrally managed through Organization > Configure > Policy objects. It is an organization-wide feature shared with all networks within the organization.
Network Objects can contain:
- IP Address
- IP Subnet (CIDR)
- FQDN and Wildcard FQDN
Network Groups can contain one of the below combinations. Network Groups cannot contain a mix of IP/CIDR and FQDN Network Objects.
- One or more IP/CIDR Network Objects OR
- One or more FQDN Network Objects.
Network Objects/Groups can be applied in the below firewall rules:
- Individual and Template Networks: Layer 3 Inbound, Layer 3 Outbound, and Failover Cellular Firewall Rules
-
Organization-wide Site to Site VPN Outbound Firewall Rules
Note:
- Network Objects/Groups cannot be applied to Group Policies.
- FQDN, Wildcard FQDN, and Network Groups with FQDN objects can only be applied to Layer 3 Outbound Firewall Rules. They cannot be applied to Failover Cellular Firewall Rules or Site-to-Site VPN Outbound Firewall Rules.
- Layer 3 Outbound Firewall Rules only support FQDN in destination section, thus Network Objects with the FQDN and Network Groups with FQDN objects cannot be applied to the source section of L3 Outbound Firewall Rules.
- Layer 3 inbound rules cannot be manually configured unless the NAT Exceptions (AKA No NAT) early access feature is enabled.
Administration
Network Objects is an Organization-wide feature. The below details the different Network Objects access for an Organization and Network Administrator.
| Organization Administrator | Network Administrator | |
| Create Network Objects/Groups | Yes | No |
| Convert Existing IP, CIDR and FQDNs to Network Objects | Yes | No |
| Access Network Objects Management Page (Organization > Configure > Policy objects) | Yes | No |
| View Network Objects via API | Yes | Yes |
| Apply Network Objects to Firewall Rules | Yes | Yes |
Configuration
Managing Network Objects
Network Objects can be centrally managed in Organization > Configure > Policy objects.
Creating Network Objects
Network Object is a label that contains either an IP Address (192.168.1.1/32), IP Subnet (192.168.1.0/24), FQDN (www.example.com) or Wildcard FQDN (*.example.com).
Note: If a Network Object is created to contain a root domain (example.com), Wildcard FQDN (*.example.com) is automatically assumed.
- To create a new Network Object, navigate to Organization > Configure > Policy Objects > All objects > Add New

- After successfully creating Network Objects, the Network Objects All Objects tab management page should look like the below.
Creating Network Groups
Network Group is a group that contains one or more Network Objects.
- To create a Network Group, navigate to Organization > Configure > Policy Objects > Groups > Add new. In the pop up menu, you will be able to type in values (IP Address, IP Subnet, FQDN or Wildcard FQDN) in the Contains field to contain in the group. For each value, you must click on the auto-suggested options (new value or existing objects) to enter the entry in the Contains field.

- For any new IP Addresses or FQDN entered, the next screen will require you to create a Network Object for the respective entry.

- After successfully creating the Network Group, the Network Objects Groups tab management page should look like the below.

Modifying Network Objects/Groups
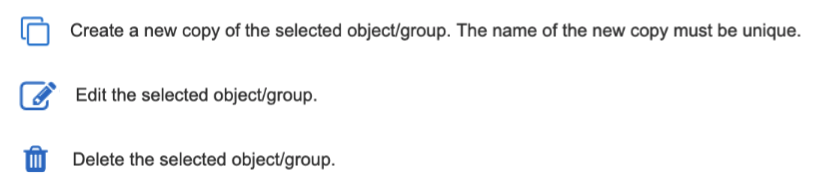
For each Network Object/Group, you have the ability to create a new copy of the existing object/group, edit and delete. To perform a specific action, please select the appropriate icon shown below.
Note: If a Network Object/Group is modified, the new changes will reflect on all firewall rules, where the respective Network Object/Group is referenced.
Applying Network Objects
Network Objects/Groups can be applied to
- Individual and Template Networks: Layer 3 Inbound, Layer 3 Outbound, and Failover Cellular Firewall Rules.
- Organization-wide Site-to-Site VPN Outbound Firewall Rules
Create a New Firewall Rule
- To create a new firewall rule, navigate to Security & SD-WAN > Configure > Firewall > Add new. Type the appropriate Network Group/Object name in the Source and Destination fields. Auto-suggestion will show existing Network Objects/Groups for you to choose from.

- If additional rules need to be added, repeat the above process. After all rules are added and click on Finish editing and Save.
Creating Network Objects/Groups within Firewall Rules
As a shortcut, Network Objects/Groups can also be created when clicking on the Source and Destination fields in the respective rule. Once a value is typed in the Source or Destination field, click on the appropriate auto-suggested option.

You will then have the ability to convert the value into a Network Object and contain it in a Network Group.

Please note that if you click on an existing Network Object, the option to contain it in a Network Group will present as well.

Modify Existing Rule
To modify an existing rule, click on  under the Actions column for the respective rule. The actions that you can choose to perform are below.
under the Actions column for the respective rule. The actions that you can choose to perform are below.

In addition, you have the ability to move a rule higher or lower in the firewall rules table by clicking and dragging on  for the respective rule.
for the respective rule.
Removing Network Object from Existing Rule
To remove a Network Object from an existing rule, click  for the respective rule and click Edit. This will enter you into edit mode for the rule. Click on the Network Object you wish to remove and hit Backspace or Delete twice on your keyboard. Hitting Backspace or Delete once on your keyboard will display the below pop up alert asking if you want to remove the Network Object. Hitting the Backspace or Delete a second time will result in removing the Network Object. After the Network Object is removed, remember to click Finish editing and Save.
for the respective rule and click Edit. This will enter you into edit mode for the rule. Click on the Network Object you wish to remove and hit Backspace or Delete twice on your keyboard. Hitting Backspace or Delete once on your keyboard will display the below pop up alert asking if you want to remove the Network Object. Hitting the Backspace or Delete a second time will result in removing the Network Object. After the Network Object is removed, remember to click Finish editing and Save.

Bulk Edit and Delete Rules
To edit or delete several rules at once, check the desired rules and click More actions > choose either Bulk edit or Bulk delete.

Converting Existing Rules to use Network Objects
It is possible to convert previously configured IP Addresses, IP Subnets and FQDNs in existing firewall rules to utilize Network Objects. To do so, edit the rule by clicking  for the respective rule and click on the IP Address, IP Subnet or FQDN. A pop up will appear asking to input a Network Object name to create a new Network Object.
for the respective rule and click on the IP Address, IP Subnet or FQDN. A pop up will appear asking to input a Network Object name to create a new Network Object.

Example of Firewall Rules using Network Objects/Groups

Compatibility
Network Objects can be applied alongside our existing VLAN Objects used in Template Networks Firewall Rules.
VLAN Objects
VLAN Objects are primarily used to represent Template created VLANs. They can be created and modified within Template Network Firewall Rules.
Note: VLAN Objects may also be used within networks that are not bound to a template.
For additional information regarding VLAN Objects, please refer to:
Managing Multiple Networks with Configuration Templates
IPv6 LAN capabilities are a requirement for VLAN Objects. VLAN objects and HA MXs (warm spare) do not work together since HA pair does not currently support IPv6. When a warm spare is added to a network, you will lose the ability to use VLAN objects and any existing L3 rules utilizing VLAN objects will be removed.
Example of Template Firewall Rules using Both Network and VLAN Objects

API
APIs can be used to create, modify and apply Network Objects/Groups to firewall rules. For a list of supported APIs, please navigate to Help > API documentation and see the Policy object groups and Policy objects sections. When creating a Network Object/Group, the Network Object/Group will correlate to an ID. This ID is an unique identifier for the created Network Object/Group. To update, delete or apply the created Network Object or Group, you will need to reference this ID in the respective format OBJ[ID] or GRP[ID]. You can see a full list of created Network Objects/Groups and their respective IDs by utilizing the API call corresponding to listing Network Objects/Groups for the entire Organization.
As of 4/1/2021, we launched new v1 Policy Object API endpoints. This allows Policy Objects to more easily introduce future Objects such as Application, Ports and etc.
The old v0/v1 Network Objects API endpoints (existed prior to 4/1/2021) will continue to function. However, these will be deprecated in the future. The exact date is still TBD. If you're using the old v0/v1 Network Objects APIs to create/modify your Network Objects, please take this time to migrate to the new v1 Policy Objects APIs.
Example of Creating a Network Object Using API
HTTP Request to create a Network Object named "Test Object" for subnet "10.0.0.0/24":
curl -L -H 'X-Cisco-Meraki-API-Key: <key>' -H 'Content-Type: application/json' -X POST --data-binary '{"name":"Test Object","category":"network", "type": "cidr", "cidr":"10.0.0.0/24","groupIds":[]}' 'https://api.meraki.com/api/v1/organizations/{organizationId}/policyObjects'
HTTP Successful Response. Note "id" correlates to the unique id of the created Network Object:
{ "id": "1234",
"name": "Test Object",
"category": "network",
"type": "cidr",
"cidr": "10.0.0.0/24",
"created_at": "2018-05-12T00:00:00Z",
"updated_at": "2018-05-12T00:00:00Z",
"groupIds": [ ],
"networkIds": [ ]}
Example of Applying a Network Object to a Layer 3 Firewall Rule Using API
HTTP Request to apply the previously created Network Object to the Source field of a Firewall Rule. Note that the ID was used to reference the Network Object (OBJ[ID] ).
curl -L -H 'X-Cisco-Meraki-API-Key: <key>' -H 'Content-Type: application/json' -X PUT --data-binary '{"rules":[{"comment":"Test Rule","policy":"allow",","protocol":"tcp","destPort":Any,"destCidr":"Any",
"srcPort":"Any","srcCidr":"OBJ[1234]","syslogEnabled":false}]}' 'https://api.meraki.com/api/v0/organizations/{organizationId}/networks/{networkId}/FirewallRules'
HTTP Successful Response:
{ "comment": "Test Rule",
"policy": "allow",
"protocol": "tcp",
"destPort": Any,
"destCidr": "Any",
"srcPort": "Any",
"srcCidr": "OBJ[1234]",
"syslogEnabled": false }



