Using special characters in WEP keys
Warning: WEP is deprecated in MR 30.X and newer firmware. Limited configuration options still exist when using the old Access control page (Wireless > Configure > Access control > View old version > WPA encryption mode) until this page is deprecated.
Please refer to WEP Deprecation on MRs for more information.
Wired Equivalent Privacy, or WEP, is a form of wireless authentication used for associating to 802.11 wireless networks. The use of special characters is disallowed when configuring a static WEP key in Dashboard as shown in Figure 1.
Figure 1. Error: - The WEP key is invalid: it must be either 10 or 26 characters long (for 64-bit and 128-bit WEP respectively) and contain only digits and the letters A through F

However, there is a workaround if the use of special characters is necessary when configuring a WEP key.
A 128-Bit WEP key is a 26-digit hexedecimal key that can also be represented by its 13-digit ASCII equivalent (Full list of ASCII equivalents can be found here). When configuring a static WEP key in the Meraki Dashboard, either form of the WEP key is acceptable. If a 13 digit ASCII key is used for WEP, this will be converted in transit to its 26 HEX representation. (The configured ASCII passphrase will still appear as what was configured in Dashboard.) If a 26 digit HEX key is used, it will be unaltered in transit.
Warning: WEP is among the older and less secure of the means of associating to wireless networks, and when possible more secure authentication protocols such as WPA2 or 802.1x authentication are recommended.
To make use of special characters in the static WEP key, follow the below steps:
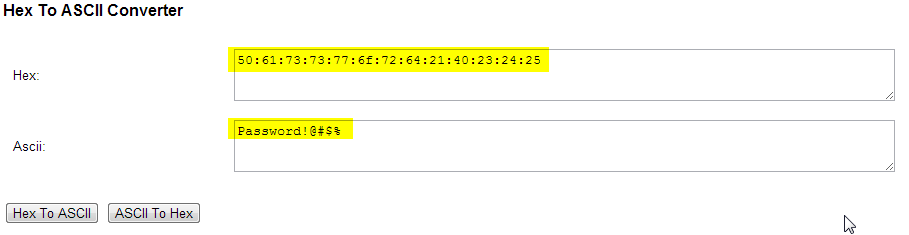
1. Convert the 13-digit ASCII passphrase to its 26-digit HEX equivalent using any free online tool.
Example tools:
http://www.branah.com/ascii-converter
2. Copy the converted 26-digit HEX value to the passphrase field in Dashboard.

3. Save changes.
At this point, users will be able to associated to the SSID using WEP with the ASCII password, even thought the configured password in Dashboard is in HEX.



