Introduction to IOS XE Based Secure Routers Managed by Dashboard
Functionality Overview
Dashboard Management for IOS XE Based Routers enables onboarding for IOS XE based Generation-2 Secure routers into Dashboard. For detailed onboarding instructions, please visit the onboarding documentation page.
When operating in Configuration Source: Cloud, management of the device must be performed by API.
Beta API Access must be enabled within the Early Access page in order to begin use.
At this time, an organization is limited to housing either MX or IOS XE Secure Routers. It is recommended a new organization is created for IOS XE Based Secure Routers to be onboarded.
Supplemental Documentation
Supported Features
Features not explicitly listed here should be considered to be not supported.
Onboarding
- Zero Touch Provisioning (Configuration Source: Cloud)
Live Tools & Monitoring
- Port Status
- Historical Device Connectivity
- Cloud CLI
- Uplink Telemetry
- WAN Status
- Device Health - coming soon
- CPU
- Memory
- Power Consumption
- Uptime
- Ping
- Traceroute
- MAC Table
- ARP Table
- Route Table
- Firmware Status - coming soon
- Reboot Device
The following live tools are available via API and require a job to be enqueued prior to operation:
- ARP Table
- Port Status
- Power Consumption
- Route Table Lookup & Route Table Summary
Configuration
- WAN Uplink Settings
- Layer 2 Interface
- Layer 3 Interface
- DHCP
- NAT
- Static Routing
- AutoVPN
- eBGP on LAN
- Firmware Upgrade
Monitoring & Troubleshooting
Live Tools
Port Status
Port Status is available under 'Security & SD-WAN' -> 'Appliance Status' -> 'Summary'
The interface describes:
- Port physical status
- Speed
- Duplex

Historical Device Connectivity
Historical Device Connectivity graph is available under 'Security & SD-WAN' -> 'Appliance Status' -> 'Summary'
The interface describes historical connectivity of the device to Dashboard. This is built based on the control session (TLS Tunnel) historical connectivity reports from the device.
Cloud CLI (read)
Cloud CLI enables read access for devices operating in Configuration Source: Cloud mode.
See Cloud CLI Specific documentation for additional details.
Cloud CLI (write)
Cloud CLI with write access is available for devices operating in Configuration Source: Device mode. This terminal provides read/write access based on user permissions.
Session logging & auditing is also provided within the Cloud CLI page. This page can be accessed via 'Security & SD-WAN' -> 'Appliance Status' -> 'Cloud CLI'

Client Details & WAN Consumption
Client Details & WAN Consumption graph provides historical consumption / usage of individual WAN Interfaces. This is available from the 'Security & SD-WAN' -> 'Appliance Status' -> 'Summary' page
The information provided is a historical presentation of bytes in/bytes out for the defined WAN interfaces.

Device Health
The ‘Device Health’ tab provides key insights into operational functionality of the device. This page is available from 'Security & SD-WAN' -> 'Appliance Status' -> 'Device Health'
This tab provides a realtime view of:
- Uptime
- CPU Load
- Memory consumption
- PoE Consumption
- Power Supply Unit status
Ping
For an overview of Ping functionality, please visit the broader Live Tools page.
Traceroute
For an overview of traceroute functionality please visit the broader live tools page.
MAC Table
The MAC table provides a readout of L2 entries entered into the table, as detected across all interfaces. The MAC Table is available from within 'Security & SD-WAN' -> 'Appliance Status' -> 'Tools'

ARP Table
The ARP table provides a readout of L3 entries entered into the table, as detected across all interfaces. The ARP Table is available from within 'Security & SD-WAN' -> 'Appliance Status' -> 'Tools'

Route table
The Route table provides real-time output of the current forwarding information base for multiple routing protocols. The Route Table is available from within 'Security & SD-WAN' -> 'Route Table'
The route table maximum display capacity is 300. Filters should be leveraged in order to reduce the overall amount of output.

Available route sources & protocols available are:
- (e/i)BGP
- Static
- Directly Connected
- Auto-Installed WAN Default Routes
Available filters are:
- Subnet
- Next Hop
- Routes/Route Protocols
Appliance Details
The Appliance Details are provided on the left nav pane when navigating to 'Security & SD-WAN' -> 'Appliance Status'
Information available includes:
- Model
- Serial Number
- Cloud ID
- MAC Address
- WAN Uplink Information
- Firmware Version
- Regulatory Information
- Device Uptime

Configuration
When removing a device from a network L3 & L2 Configurations are disabled and will need to be reapplied manually.
Firmware Upgrade
Firmware upgrade functionality is described within the following documentation.
WAN Uplink and DNS
WAN1 and WAN2 IP Addressing information can be configured via API only. Available parameters include:
- Static
- IP Address
- Netmask
- Gateway
- DNS
- Dynamic
When configuring a combination of static & dynamic addressing, DNS shall be appended to the existing list. In a scenario where DNS is provided by both static and dynamic configurations, the primary DNS shall be the static entry with the dynamic entry being secondary.
Interface List
A list of interfaces and their current configuration(s) may be obtained by API only. The response shall indicate:
- Port configuration & available configuration modes
- Flex, L2, L3
- Mode
- WAN/LAN
- Trunk/Access/L3 Transport configuration
Layer-2 Interface: Trunk or Access
Layer 2 port settings can be obtained (GET) and modified (PUT) for all or individual ports via the endpoints (Partial updates are permitted)
NOTE:
- Access: Only “Open” Access Policies are supported
- Trunk: To drop untagged traffic, the native vlan ID must be omitted from the list of allowed VLANs.
VLAN and DHCP
Retrieve and configure VLAN and DHCP settings on a network appliance
Layer-3 Interface
Retrieve and configure L3 interfaces with Static IPv4 address and subnet.
NOTE: IPv6 address configuration not supported
NAT
Configuration of NAT is available for WAN interfaces. All traffic which egress' this interface shall inherit the configured functionality.
Available configurations are:
- NAT Enabled per WAN
- NAT Disabled per WAN
Static Routing
Configuration of static routes is available for LAN routing. Configuration includes next hop and destination subnet.
Static routes inherit the LAN transport interface's behavior for VPN Enablement/Disablement. If the source interface used for a static route is VPN Enabled, the associated downstream subnet will be implicitly enabled as well.
Object tracking, or IP SLA, is not available for static routes at this time.
AutoVPN
AutoVPN, a seamless fabric and overlay technology, is available for IOS XE Based Secure Routers in Dashboard. For additional information regarding AutoVPN's use cases, configuration within the UI, and respective functions, please visit the AutoVPN Guide.
AutoVPN may be configured via the UI or via API.
- AutoVPN on IOS XE Devices operates in a common manner for VPN Registry enablement.
- Hub to Hub routing is not available for AutoVPN
- When leveraging multiple WAN Uplinks, VPN tunnels will be built across all available uplinks.
- ECMP (Load Balancing) is not currently available. The primary interface, configured statically as the highest ID L3 interface, shall be considered primary WAN. Traffic shall be sent via the primary WAN when available.
For a detailed review of AutoVPN Configuration relative to IOS XE, please visit the AutoVPN for IOS XE Configuration Guide.
AutoVPN on IOS XE Devices leverages a standards based IKEv2 Based IPsec implementation. Key Security Association details are below:
IKE SA Parameters:
- Port: 500/4500 (NAT-T Forced)
- Lifetime: 8 hr
- Encryption: AES-GCM-256
- Pseudo-Random Function: SHA256
- Authentication: Dashboard Derived PSK (unique per endpoint pair)
- UDP/ESP Encap (Tunnel)
- DHG: 21
- DPD Frequency: 10s
- DPD Teardown Threshold: 3
- MTU: 1400, Fragmentation Enabled
IPsec SA Parameters:
- Lifetime: 4 hr
- Encryption & Integrity Checking: ESP-GCM-256
- Mode: Tunnel
- Replay Protection: 1024
- PFS: DHG 21
AutoVPN Routing leverages iBGP for prefix redistribution.
- Spokes
- A BGP Community string is applied to hubs based upon their selected priority
- A route map applies weight, matching the community string, to prefixes as they are received on the spoke
- Example: Hub Priority 1 - All prefixes received have weight 990 applied
- Example Hub Priority 2 - All prefixes received have weight 990 applied
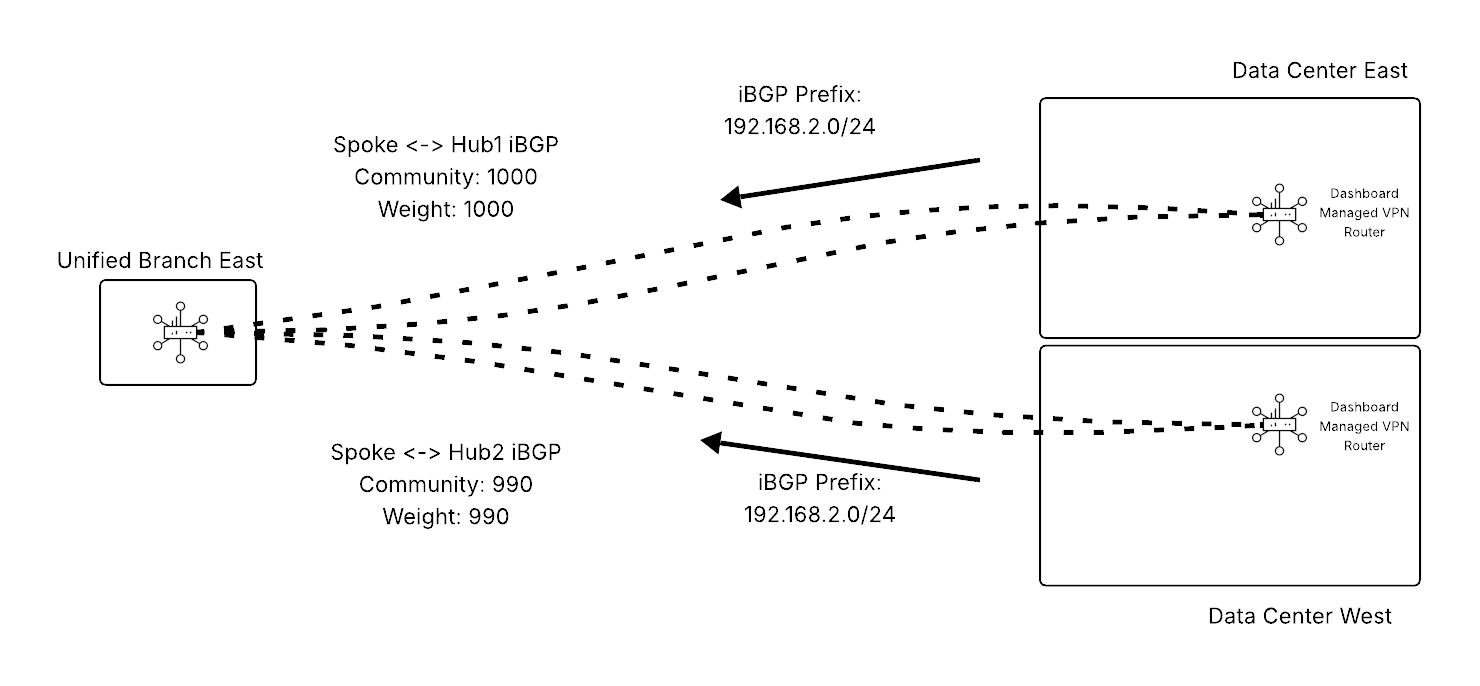.png?revision=1)
- Hub
- Spokes send a community string attribute with routes as they are advertised to hubs
- A route map applies local preference, matching the community string, to prefixes as they are received on the hub.
- Example: Hub Priority 1 - All prefixes received have local preference 1000 applied
- Example: Hub Priority 2 - All prefixes received have weight 1000 applied
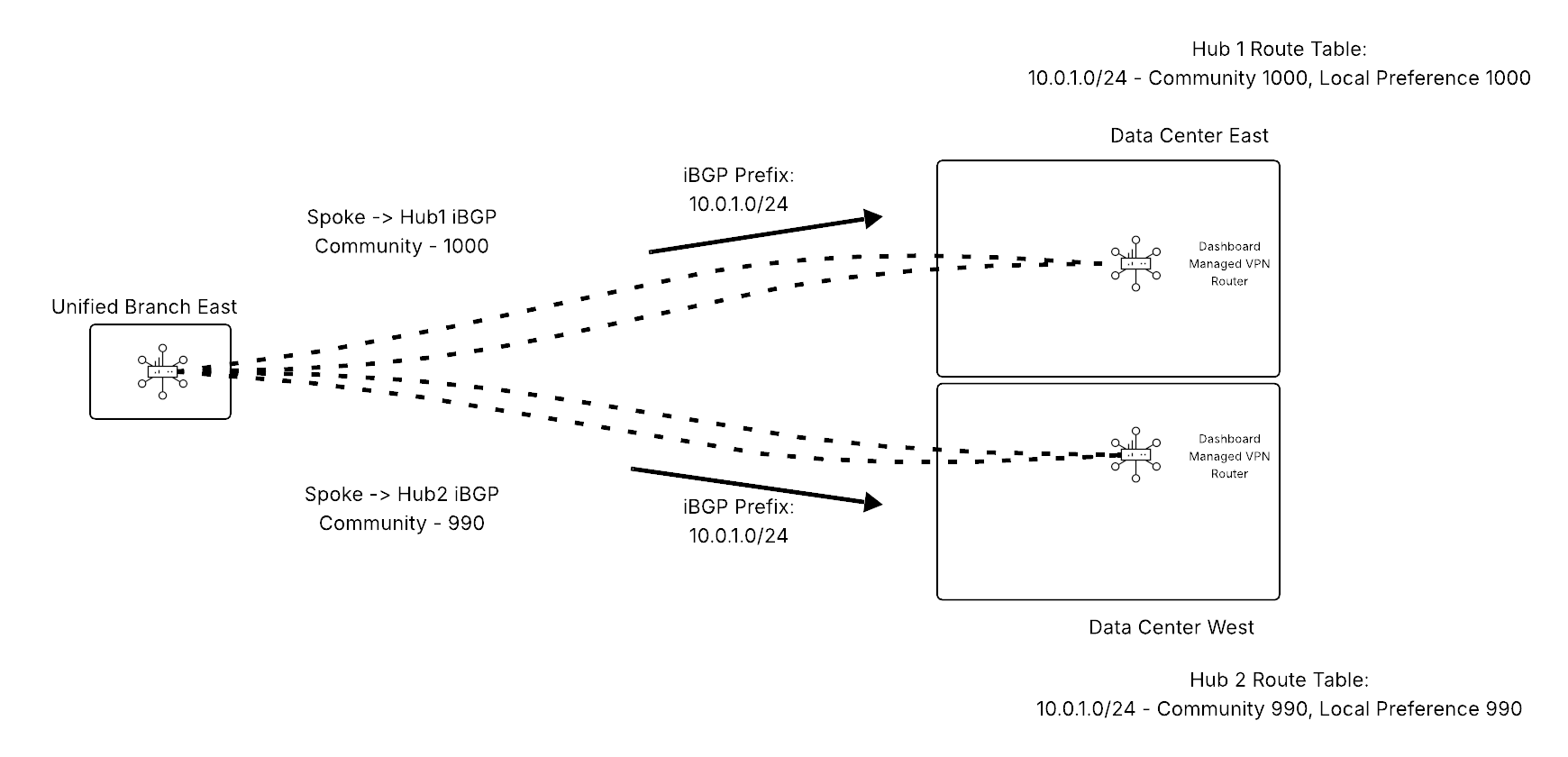.png?revision=1)
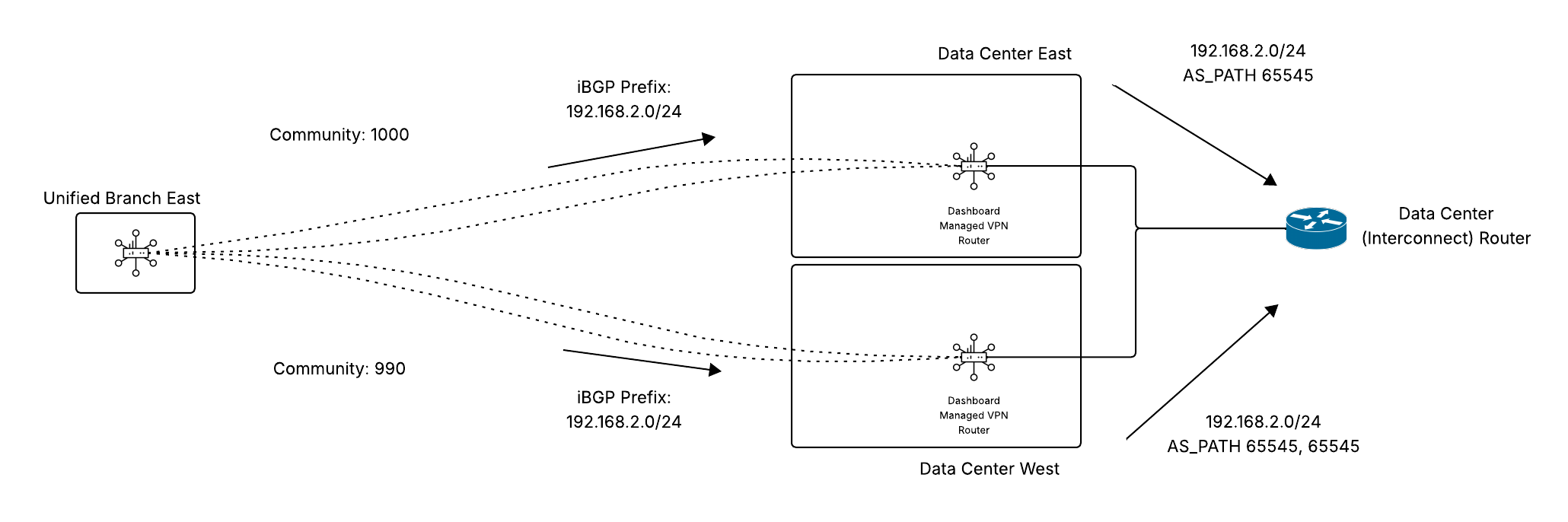
- Hub eBGP Redistribution
- AS_PATH Prepending is performed when redistributing prefixes into the eBGP Autonomous system.
- The number of prepends is based upon the hub priority configured for the spoke.
- Example: Hub Priority 1 - All prefixes redistributed have no AS_PATH Prepending applied
- Example: Hub Priority 2 - All prefixes redistributed have 1x AS_PATH Prepending applied
eBGP on LAN
eBGP on LAN, permitting a hub to learn and redistribute prefixes into and out of the AutoVPN Autonomous system, is available by API Configuration only.
- eBGP on LAN is available for devices operating as a hub only.
- Up to 10 eBGP Neighbors can be enabled

