Cellular Data Management with Systems Manager
Systems Manager can be used to automatically track and audit cellular data usage across your devices, as well as apply policies based on cell data limits through the use of dynamic security tags.
Monitoring Cellular Data Usage
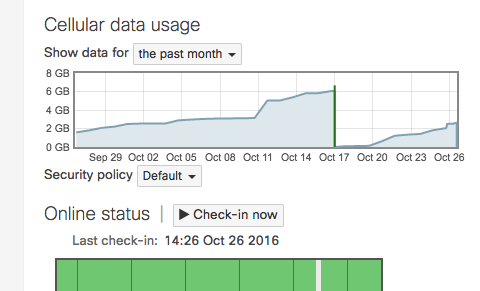
By default, usage will reset the first day of every month, although this can be customized under Systems manager > Configure > General. An individual client's cellular data usage can be monitored in the Monitor > Devices > Client details page (clicking into the client), directly above the Check-In Status area.
The usage reported by SM is best effort. Dashboard may under report or over report data usage in comparison to service provider statements. Consult your service providers data usage for the most accurate data.
On iOS devices, the Systems Manager app needs to be running in the background to update Dashboard and report the latest cell data usage.
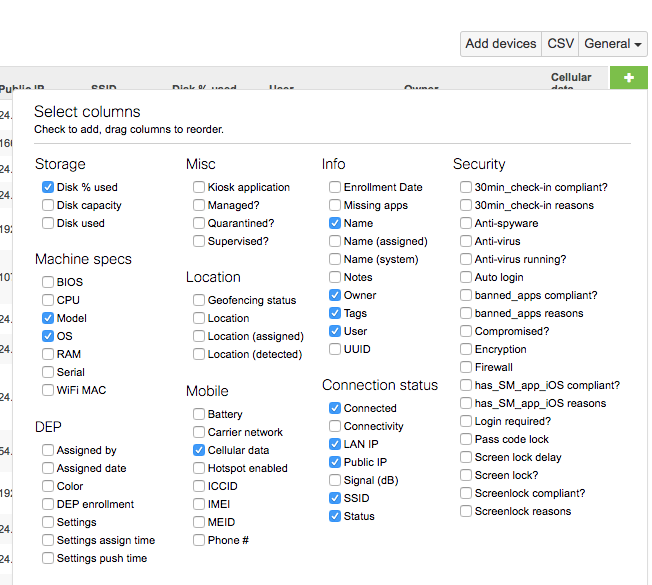
Clients can be monitored in bulk under Systems Manager > Monitor > Clients page by adding the 'Cellular data' column.
Managing Cellular Data Usage
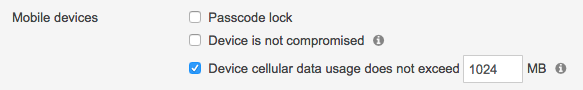
Security policies can be built around cell data usage under Configure > Policies. The corresponding security policy tag generated can then be used to scope applications and profiles. This allows admins to automatically remove non-essential apps or place additional restrictions on users that violate their data quota. For more information, see the security policies article.
To alert end users prior to data overages, considering setting the security policy limit to be 90% of their monthly quota. This way, Dashboard admins will be alerted when users are nearing their limit and can send notifications directly through Systems Manager (clients list or client details pages) to warn them.
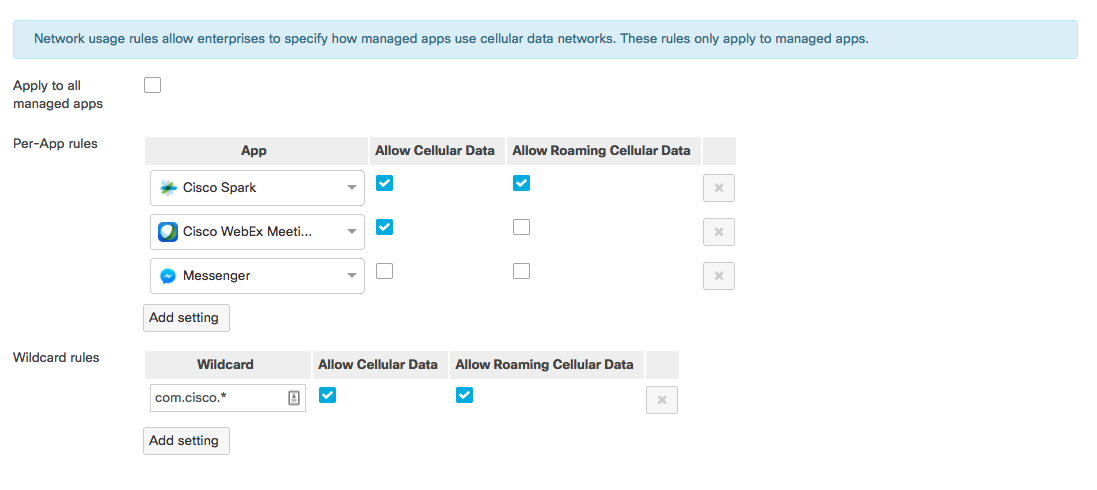
Network Usage Rules Payload
On iOS devices, roaming and cellular data can be enabled or disabled for managed applications either on a per-app basis, or through the use of wildcard bundle identifiers. This can be used in conjunction with security policies tracking cellular data usage. For example, a policy can be created to detect when an end user hits 90% of their monthly cellular data usage. The policy's violating tag can then be used to apply a profile disabling cell data for non-essential applications upon hitting this limit to help prevent overages.
To configure this payload, navigate to Systems Manager > Manage > Settings > Add settings > More iOS > Network usage rules.