vMX Setup Guide for Amazon Web Services (AWS)
On November 5, 2020, we discontinued our old vMX offer on the AWS Marketplace. For any issues that are not firmware related, AWS will not provide support for the old vMX100 offer after February 3, 2021.
Cisco Meraki will continue to support the vMX100 SKU through December 22, 2027, per the EoS notice.
Customers can deploy the current vMX-S/M/L/100 SKUs using the new vMX offer on the AWS Marketplace.
A 4 Core vCPU instance type is required for IDS/IPS (SNORT) functionality on vMX-M. The following AWS instance types will not be able to run the feature:
- c5.large
- m4.large
If you are currently using these instance types and but require IDS/IPS (SNORT) functionality, we recommend changing your vMX-M to a c5.xlarge instance instead.
Overview
This document is a walkthrough for setting up a virtual MX (vMX) appliance in the Amazon Web Services (AWS) Marketplace (including China). After completing the steps outlined in this document, you will have a virtual MX appliance running in the AWS Cloud that serves as an Auto VPN termination point for your physical MX devices.
Key Concepts
Before deploying a vMX, it is important to understand several key concepts:
Concentrator Mode
All MXs can be configured in either NAT or VPN concentrator mode. There are important considerations for both modes. For more detailed information, see the article on concentrator modes.
One-Armed Concentrator
In this mode, the MX is configured with a single Ethernet connection to the upstream network. All traffic will be sent and received on this interface.
NAT Mode/Secure Cloud Gateway
In this mode, any traffic coming over to LAN port of the vMX will be NATed to the vMX's WAN IP as it egresses the vMX, while also maintiaining its ability to act as a hub for Site-to-Site and Client VPN.
As of MX 19.1, vMX will also support all other NAT Mode and Security features that you would find on a physical MX, enabling the vMX to act as a Secure Gateway for your cloud-hosted resources. Please look at vMX NAT Mode Use Cases and FAQ for more information.
Change in default behaviour
All new vMXes deployed post October, 31, 2022 will be deployed in Routed/NAT Mode Concentrator by default, existing vMX deployments will not be affected. If you wish to use the vMX in passthrough mode, please change the deployment settings to Passthrough or VPN Concentrator mode from the Security & SD-WAN > Configure > Addressing & VLANs page.
VPN Topology
There are several options available for the structure of the VPN deployment.
Split Tunnel
In this configuration, branches will only send traffic across the VPN if it is destined for a specific subnet that is being advertised by another MX in the same dashboard organization. The remaining traffic will be checked against other available routes, such as static LAN and third-party VPN routes, and if not matched will be NATed and sent out the branch MX unencrypted.
Full Tunnel
In full-tunnel mode, all traffic that the branch or remote office does not have another route to is sent to a VPN hub.
AWS Cloud Terminology
This document will make reference to several key AWS-specific terms and concepts.
AWS
Amazon Web Services is a hosting platform that allows organizations to host infrastructures and services in the cloud.
VPC
A virtual private cloud is a virtual and private network within the AWS infrastructure. A VPC has a block of associated IP addresses, which can be subdivided into multiple smaller subnets.
EC2
Elastic compute cloud is Amazon's virtual and cloud-based computing infrastructure. EC2 allows you to run virtual machines within your VPC. A virtual machine running on the EC2 platform is commonly referred to as an EC2 instance.
Additional Information
Please refer to the AWS glossary for a dictionary of cloud terminology on the AWS Cloud platform.
Meraki Dashboard Configuration
Begin by creating a new Security Appliance network in your organization. If needed, please refer to the guide on creating a new network in the Meraki dashboard.
1. Add license(s) to the Meraki dashboard
To complete the vMX Meraki dashboard configuration, a vMX license must be available for use in your organization.
If your organization has already reached its vMX license limit, you will be unable to create new vMX networks until a vMX network is deleted or additional vMX licensing added.
If you do not have access to a vMX license or require additional vMX licenses, please reach out to your Meraki reseller or sales representative.
2. Create a "Security appliance" network type:

3. Assign vMX type to network
Once you have created the "Security appliance" network and added the appropriate license you will be able to deploy a new vMX to your network by clicking on the 'Add vMX' button.

4. Generate the authentication token
Before generating the token, please verify the firmware is configured for MX 15.37+. If the vMX network firmware is set to anything below that, the upgrade will not occur.
After you add the new vMX to your network, navigate to Security & SD-WAN > Monitor > Appliance status and select “Generate authentication token” to generate the token for the AWS user-data field.

5. Copy the newly generated token and save it.
The newly generated token will be used in the "System Configurations" section when creating a new AWS Cloud instance.
The authentication token must be entered into the AWS Cloud instance within one hour of generating it, otherwise a new token must be generated.
AWS Setup
This section walks you through configuring the necessary requirements within AWS and adding a vMX instance to your virtual private cloud (VPC). For more details on setting up a VPC and other components, refer to Amazon's AWS Documentation.
Accessing the AMI
Click to access the AMI. A screenshot of the AWS Marketplace listing is included below:

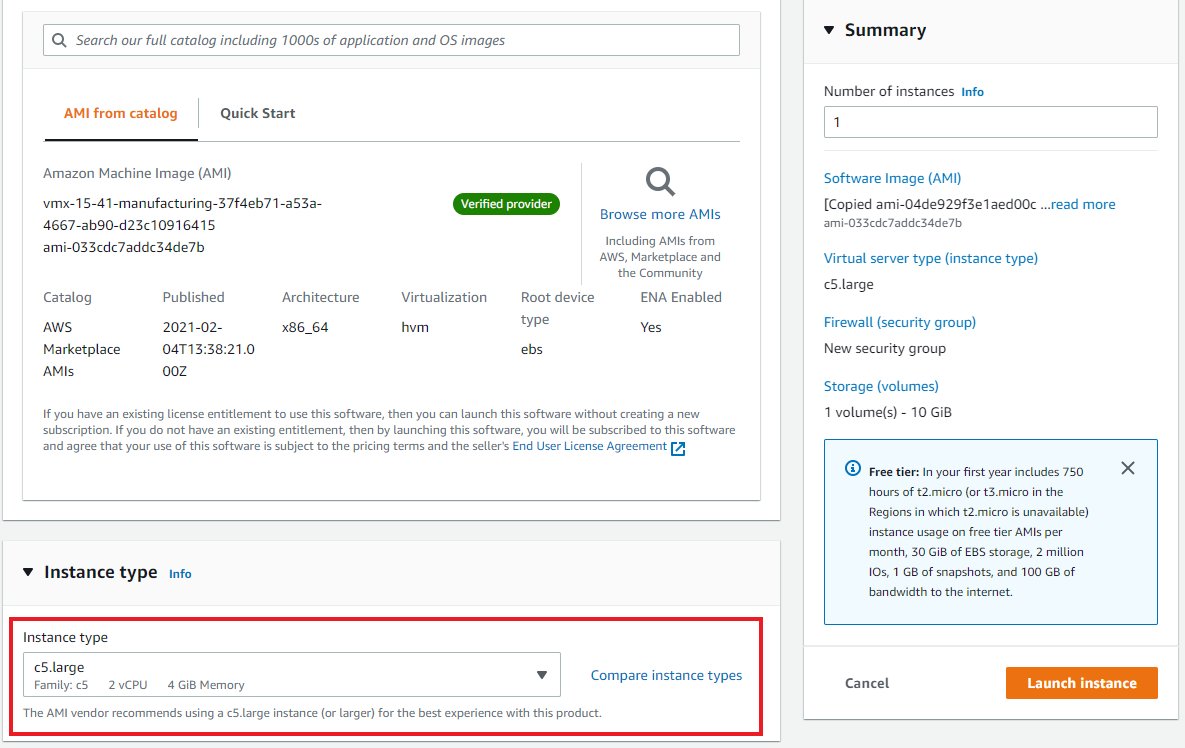
Select the EC2 instance type and the region to launch the EC2 instance in. This should match the availability zone your VPC resides in.
| vMX Type | EC2 Instance Type |
| vMX-S | c5.large |
| vMX-M | c5.large |
| vMX-L | c5.xlarge |
- Running EC2 instances has an AWS infrastructure charge. Please be mindful of this when launching your instances. The charge can be found in the cost estimator table to the right of the instance type selection.
When using an incorrect EC2 instance type, the vMX device might boot but fail to reach the dashboard.

Click the "Continue to Subscribe" button to configure and finalize the vMX deployment.
Configuring the EC2 Image
After continuing, you will be prompted to configure the EC2 instance settings.
For "Choose action" option select the "Launch through EC2" and click "Launch."

Choose the EC2 instance type
| vMX Type | EC2 Instance Type |
| vMX-S | c5.large |
| vMX-M | c5.large |
| vMX-L | c5.xlarge |
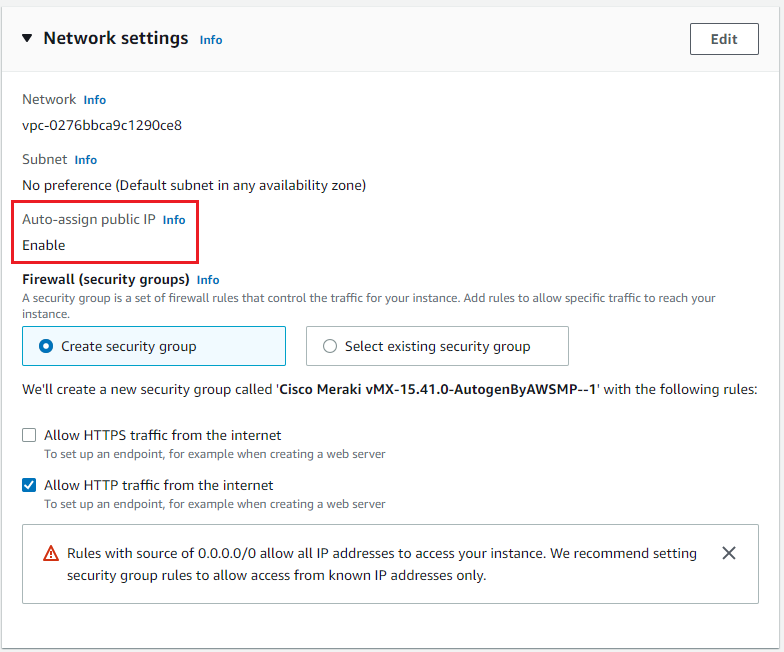
Scroll down to the network settings.
Select the VPC and the subnet the instance will be a part of and make sure the "auto-assign public IP" is enabled.
Scroll down to "Advanced Details" enter the vMX authentication token from the dashboard in the user data field.
The authentication token must be entered into the AWS Cloud instance within one hour of generating it, otherwise a new token must be generated.
Steps that need to be taken to generate the vMX authentication can be found in the Dashboard Configuration section
Metadata version 2 is not supported at this time. Using Metadata V2 can result in 'Invalid Token' error message.
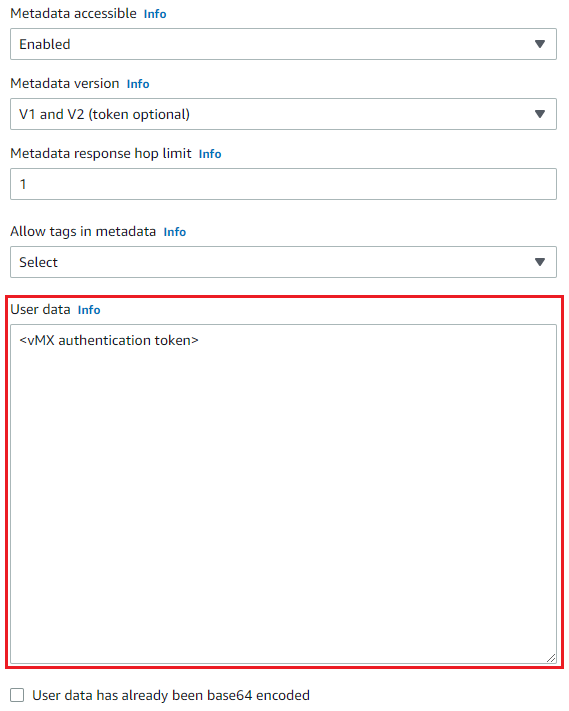
Note: the carrot "<>" brackets are to be omitted from your vMX auth token
Click "Review and Launch" to finish creating the instance.
It may take several minutes before the software subscription completes and the instance launches.
After the instance has launched, the Source/Destination check must be disabled for the vMX.
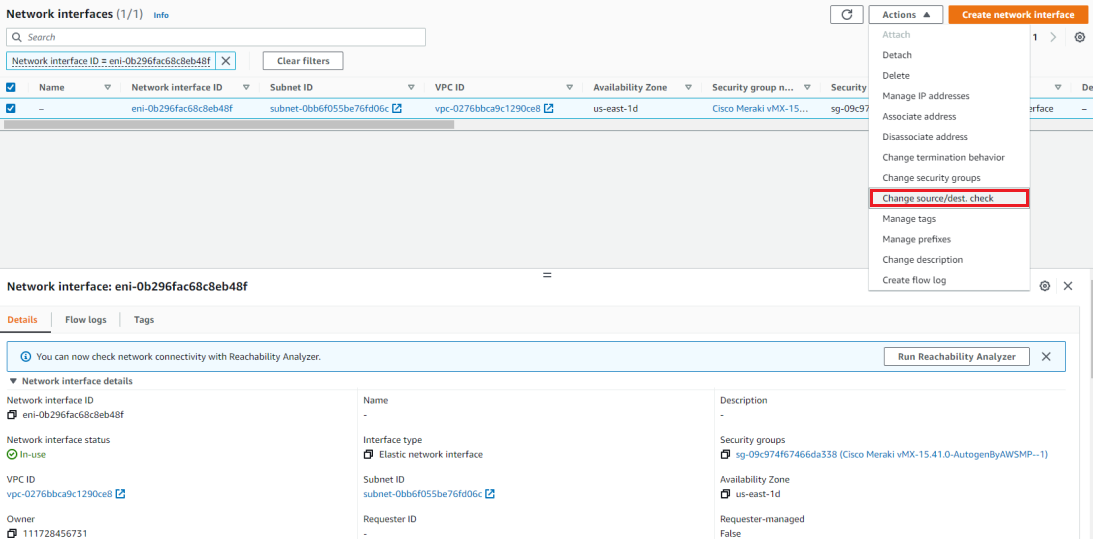
Select the network interface of the newly created vMX instance.
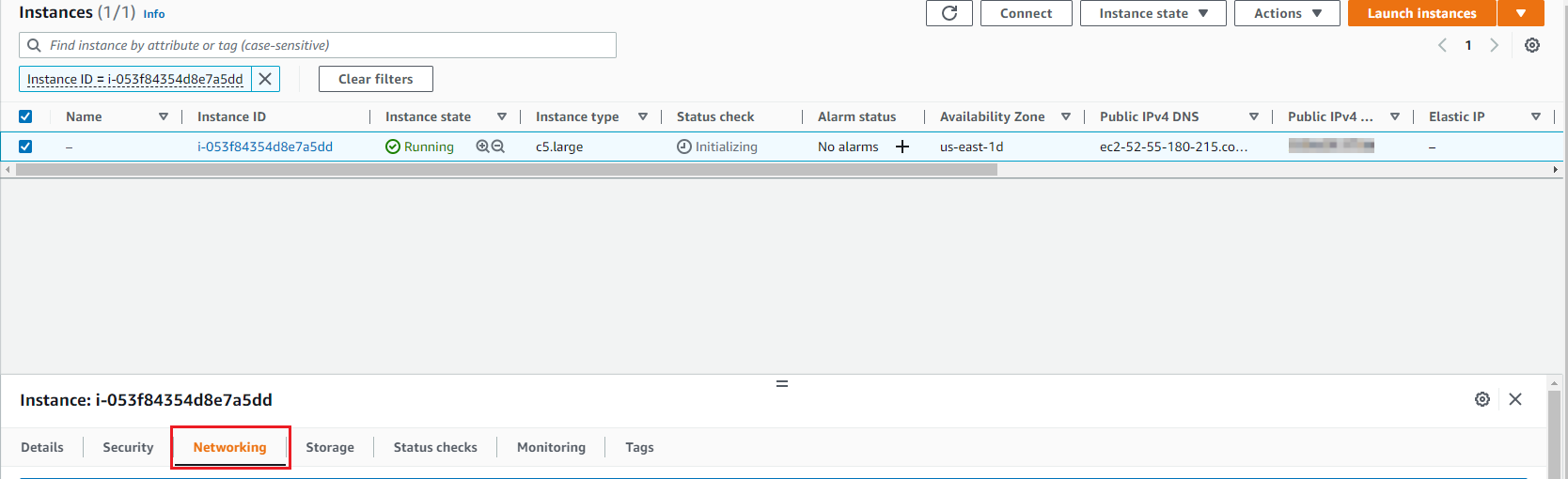
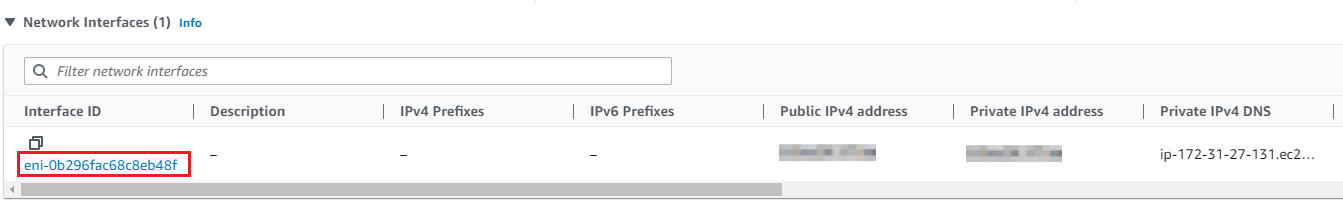
Disable the source/destination check for the network interface and click "Save."

Please see the Help > Firewall Info page for information on connections that need to be allowed upstream to provide dashboard connectivity.
Additional VPC Configuration
The virtual MX appliance will allow for site-to-site VPN connectivity using Auto VPN between AWS and other remote MXs. In order to have proper bidirectional communication between remote subnets that are terminating into AWS via the vMX and hosts within AWS, the VPC routing table must be updated for the remote Auto VPN-connected subnets.
To do this, navigate to the "VPC" dashboard in AWS, and follow the steps below:
- Click on "Route Tables" on the left-hand side.
- Find the route table associated with the VPC or subnet the vMX is hosted in (you can quickly filter the list by typing in your VPC ID or name in the search box).

- Click on the route table in the list to select it, then click on the "Routes" tab in the details pane below the list of routing tables.
- Click the "Edit" button.
- Click the "Add another route" button at the bottom of the route table.
- In the "Destination" column, add the routes available via Auto VPN.

- In the "Target" column, select either the Instance ID or Network Interface ID of the vMX.

- Repeat steps 5-7 for each network available via Auto VPN and Client VPN if applicable. You may want to use a summary address.
Below is an example of a vMX route table that lists the remote AutoVPN subnets. If return routes for these subnets are not added to the AWS VPC route table via the steps listed above, bi-directional communication between hosts in remote AutoVPN subnets and AWS resources will not occur, as return traffic will not be routed to the vMX.

AWS applications such as Amazon Cloud Watch and Systems Manager Agent (SSM Agent) is currently not supported to be used with vMX's.
Troubleshooting
The most common problem people face when deploying a vMX is getting it provisioned and online in their Meraki dashboard in the first place. New troubleshooting/diagnosis messages have been added to the vMX console screen now so you can identify what went wrong during the provisioning process.
When the vMX boots it will execute the following steps during its initial provisioning process:
- Obtain user-data (vMX auth token)
- Authenticate with the dashboard (using auth token)
- Connect to dashboard
Obtain User Data and Authenticate to Dashboard
Once a vMX has successfully connected to a network, it will then attempt to obtain its user data (vMX auth token). There are different user-data mechanisms in each platform that the vMX currently runs on to provide the token to the vMX. In AWS, Azure, GCP, and Alicloud there are user-data fields in the VM configuration where this can be provided.
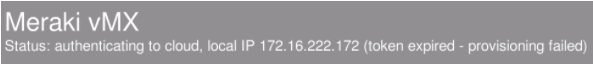
Token Expired
vMX auth tokens have a lifetime of only one hour for security purposes. If you see the following message on your vMX console it means the token you provided is no longer valid.
If the Autnentication token needs to be re-entered while the vMX instance is running, you can do the following steps to update it:
- Go to the instance in AWS
- Stop the instance
- Go to Actions > Instance Settings > Edit User Data
- Under New user data, select Modify user data as text, and enter the newly generated authentication key
- Save and restart the instance
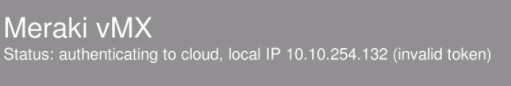
Invalid Token
If the token provided is incorrect in any way the "invalid token" message is displayed on the console.
Unable to Reach Meraki Dashboard
If the vMX is unable to reach the dashboard on TCP port 7734 then the initial provisioning phase will fail and an "Unable to reach Meraki Dashboard" message will be displayed on the console (check the firewall information page for a list of all the firewall rules needed for the Cisco Meraki cloud communication). Please refer to the document on correct ports/IPs that need to be opened for Meraki dashboard communication.
Note: Please ensure that the VPC route table is able to get out to the internet.
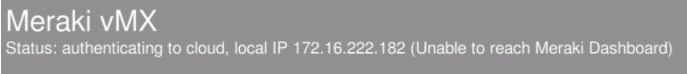
Note: For any of the following above (Token Expired, Invalid Token, Unable to reach Meraki Dashboard), you may also look to view the instance screenshot, right-click on EC2 instance > Monitor and troubleshoot > Get instance screenshot to view the status. Other resources from AWS:
No "Add vMX" Button
When navigating to Security & SD-WAN > Monitor > Appliance Status, if there is no "Add vMX" button, please ensure the following two conditions are met:
- You have available vMX licenses in your license pool.
- You have created a "Security appliance" network type.
Please note that Meraki support does not troubleshoot AWS Cloud-specific firewall rules and deployments.
Known Issues
Deploying vMX100 on m4.large
Issue: vMX100 deployed using a m4.large instance type does not handle user data correctly and the vMX fails to connect to the dashboard. A "no token provided" message is shown on the instance screen shot.
Resolution: Based on the desired firmware version, one of the following resolutions can be applied:
- 15.37+ firmware: If the desired firmware version is 15.37+, deploy the vMX100 with a c5.large instance type instead of m4.large; c5.large, also provides better performance than the m4.large instance type at the same cost
- 14.x firmware: If vMX100 is to be deployed on 14.x firmware, do the initial deployment using a c5.large instance type and once the vMX has successfully checked into the dashboard switch to m4.large instance type. Steps to change the instance type are listed below.
- Stop the vMX instance from the AWS console select "Change instance type" under instance settings

- Update the instance type to m4.large and restart the instance
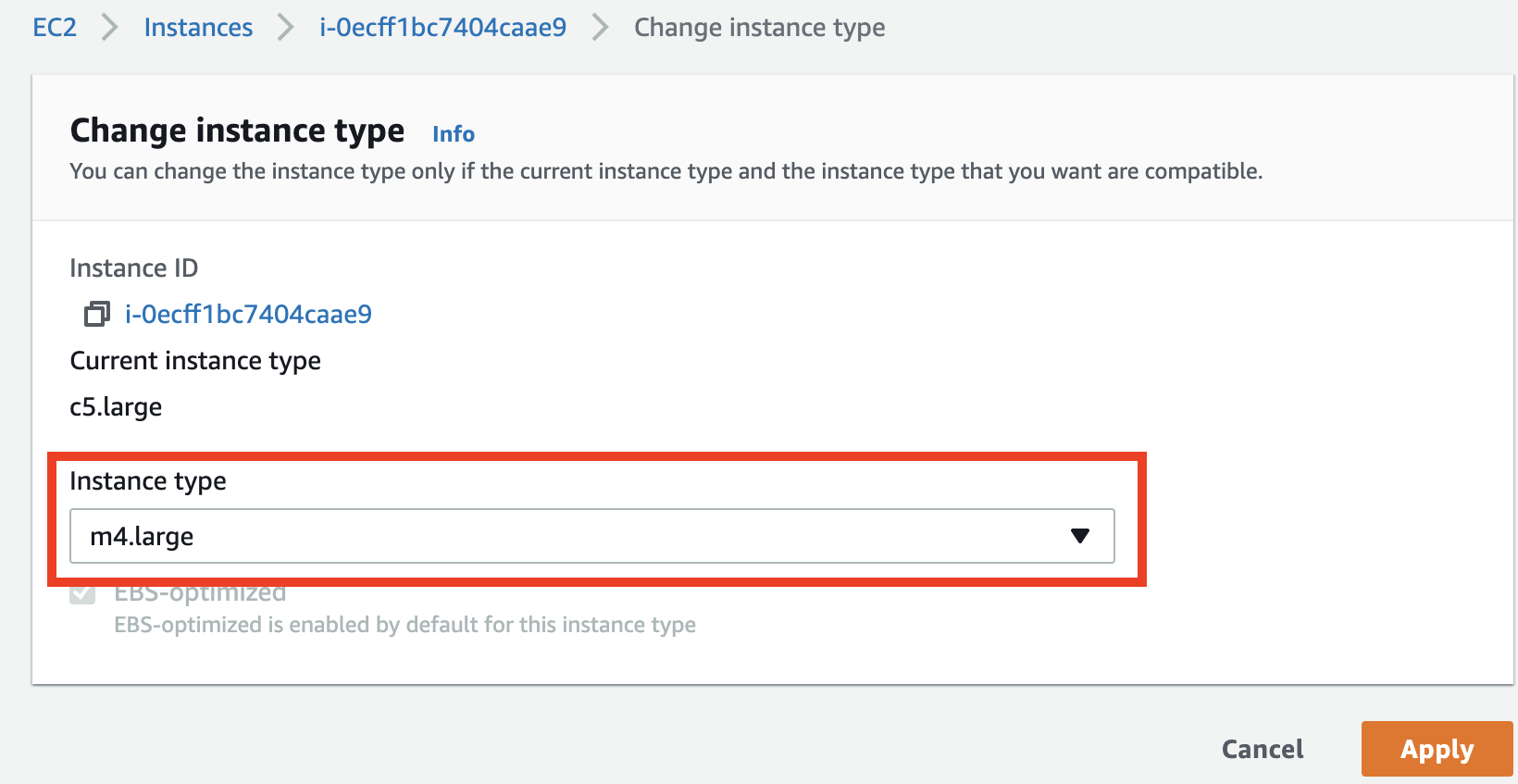
- Stop the vMX instance from the AWS console select "Change instance type" under instance settings

