Clients Usage Page Overview
Click 日本語 for Japanese
The Clients usage page on MR Access Points, MX/Z1 Security Appliances, and MS Switches tracks clients that are connected to your Cisco Meraki network with a customizable interface for filtering specific device types and traffic. It shows how the network is being used and by which client devices, and can be filtered by a two-hour, day, week, or month time interval. To view the Clients usage page, go to Network-wide > Monitor > Clients in the Meraki dashboard.
Learn more with this free online training course on the Meraki Learning Hub:
Clients Overview
The Clients page includes the following features:
- A Summary graph displaying network bandwidth usage and how it has fluctuated over a given time span.
- The list of connected clients.
- A Search function for clients by MAC address, operating system, device type or NetBIOS/Bonjour name. (For details, see the Search tool section below)
- Zoom control, which enables the administrator to see only those clients that have been connected within the specified time span. You can adjust the time span by clicking on 2 hours, day, week, or month.
- A customizable client device list with a variety of available information columns. Sort columns by clicking on a column header. Add or remove columns by clicking Columns and shifting options in or out of the Displayed columns window.
- Mouse over a row in the device list to see a new line appear in the usage graph. This line depicts the fraction of total bandwidth that the highlighted device used.
- Export list data in XML format for further processing and analysis outside of the Dashboard. Click Download as XML to retrieve the data. Most spreadsheet programs, such as Microsoft Excel, can open an XML file.
Navigating the Clients List
The clients list displays helpful information about client status, network usage, operating system, IP and MAC addressing, and additional statistics that you can choose to display by adding columns. A client will only appear in the list once it has passed traffic. If a device, such as a LAN printer, does not pass any traffic, then it will not appear in the list.
Clients appearing on the Clients usage page will display their current status to indicate if they are currently active, as seen below in Figure 1. The activity threshold for a client is one minute. If a client does not pass traffic for longer than one minute, then the client will no longer be considered active. The status icon for an inactive client will appear grey. Additionally, the Last seen column for a client displays the last time that client was seen on the network. An active client will have a value of "now" in the Last seen column, as seen below:

If you are using the combined Dashboard view, then the client status will also display the type of connection (wired or wireless) that the client is currently connected to. If the client is not currently online, then the type of connection that the client was last connected to will be shown. The connection statuses below show both wired and wireless clients:

Note: On SSIDs using Meraki DHCP, clients are identified by IP address rather than MAC address. This can result in multiple entries for a single client, all with the same MAC address, but different IP addresses. This can cause the Dashboard to display multiple clients associated with different IP address and the same MAC as illustrated below:

Filtering the Clients List
The list of clients can be customized based on time intervals, type of access, and SSID. To change these parameters, use the appropriate drop-down menu at the top of the screen.
Time intervals allow you to view clients that have been active during a specific period of time. The time drop-down menu features common intervals, as seen below:

You can also specify the type of clients that you wish to view, as seen below. This includes filtering clients seen by a specific device type (wireless, switches, etc), clients on a specific SSID (wireless only), or clients with a policy (allow listed, blocked, or group policy) applied to them.

Searching for Clients
You can search for a client in the current client list by using the search tool. You can search by any term, and the search tool will attempt to match your query across all fields. You can also specify multiple parameters by clicking on the arrow in the Search clients box, as seen below:

Modifying Columns
The Client usage list can be further customized by adding additional columns to provide more insight into traffic on your network. To add or remove columns, you can click on the + sign and select the columns that you want to appear, as seen below. To move columns, simply drag the column header and drop it into a new location.

Exporting Client Information
List data on the Clients page can be exported in XML or CSV format, by clicking the Download as button and selecting either format option.
This features of exporting will only be available for IPv6 logs and will only be available to click if the client has an IPv6 address.
Client Details
You can click on a particular device in the client device list to obtain additional information about the device. This page provides details about the client device such as the device's network usage, as well as its MAC address, IP address, hostname etc...For additional information, see our Client Details Page Overview Documentation.

(MR 33.1.1) Apple Analytics/WPA3 in Solicited Beacon
Overview
We are implementing a firmware update to address evolving limitations in how Apple devices share analytics and client details on wireless networks. With the release of iOS/macOS 26+, Apple has significantly tightened privacy controls, requiring a shift in how our infrastructure requests telemetry data.
The Challenge
Previously, Apple devices provided unsolicited beacon reports. However, Apple has introduced the following changes:
- Solicitation Required: Apple devices will now only send device analytics when they receive a solicited beacon request from an AP broadcasting a 802.1x SSID.
- Network Restrictions: For devices running iOS/macOS 26+, Apple has ceased sending device information entirely on non-enterprise (non-802.1X) networks.
- Visibility Gap: Without these updates, network administrators will face significant limitations in monitoring and managing Apple hardware connected to 802.1X SSIDs.
Technical Changes & Implementation
To maintain visibility and support for Apple analytics—specifically for WPA3 and iOS 26+—the following firmware adjustments have been made:
- 802.11k Behavior Update: We have modified the 802.11k beacon measurement request behavior. The infrastructure will now actively solicit reports to accommodate devices that no longer provide them automatically.
- 802.1X Enhancement: MR 33.1.1 firmware enables connected Apple devices on an 802.1X SSID to securely share client details through these solicited channels.
Managing Clients
The Clients page offers a number of options to manage your clients, individually or in bulk, as outlined below:
Changing the Policies Applied to a Client
You can change the policy that is applied to a client or group of clients by using the Apply policy menu on the Network-wide > Monitor > Clients page in the Dashboard. Clients can be given normal, allow listed, or blocked access. You can also apply Group Policies and apply different policies based on the SSID that the client is connected to. For additional information, please see the Block Listing and Allow Listing Clients documentation.
Note: Switches cannot apply group policies to a client, this applies to access point and security appliance clients.
To change the policies applied to a client:
- Check-mark one or more clients in the client list.
- Click the Policy button.
- Select your desired policies, as seen below:

- Click Apply.
Adding a Client
The following steps below explain how to add a client. These steps are only available for Organization Administrator in wireless and combined networks.
To add a client to the client list:
- Click the Add client button.
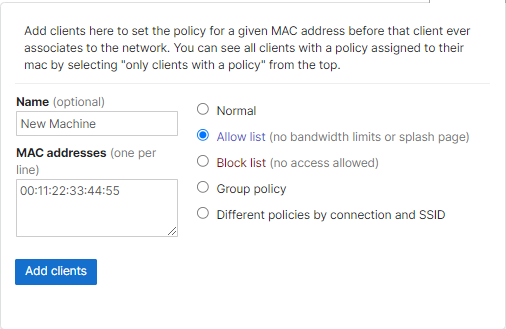
- Fill in the client's name, MAC address, and access policy. The image below shows the Add new devices tab:
- Click Add clients.
Please note that:
If the Normal policy has been applied then the client will not appear in the all clients view until it has connected to the network.
If any non-Normal policy has been applied then you can use the all clients with a policy view to see a client that you have manually added but has not yet joined the network.
Troubleshooting
Only One Client Device Is Listed in the Clients List
If there is a Layer 3 switch or a router on the LAN side of an MX then only 1 device will be seen on the Clients page even though there may be multiple computers or other devices connecting through that device.
The MX security appliance by default tracks client devices based on their MAC addresses, which means that the client devices should be discoverable on a Layer 2 level.
There are various client tracking options to avoid this behavior, please visit the Client Tracking Options document for more information.
The Client Is Offline, but the Client Details Shows It Is Active with an Online Status
Clients list data is aggregated over time and therefore the information is not ‘live’, thus there will be a slight delay to a client’s online/offline status. This data is automatically refreshed every few minutes.
Wired clients that had transferred data in the past 5 minutes should appear online. Verify that the “Last seen” timestamp is within the last 5 minutes to ensure the client reflects the proper status.
Wireless clients' online/offline status will be dependent on their association to a Meraki wireless network.
Clients List Displays Zero Usage for a Client, Though the Client Is Passing Traffic
To ensure useful data usage and traffic analysis, certain types of client traffic are filtered and are not counted toward their network usage. Usage information is recorded differently depending on the network layer the client is operating at. Examples of such traffic are:
-
Unauthorized clients (e.g.: Unauthorized by RADIUS, or clients that are operating behind a Splash or Captive Portal)
-
DNS
-
DHCP
-
ARP
Note: Wireless clients in these cases will display as connected with zero usage for as long as the Access Point confirms they are Associated. The above does not apply to switch clients.
Network Usage Does Not Match the Usage Seen on the Clients Page
The network usage seen on the device details page might not always match the usage seen on the Clients page.
The network usage includes only outgoing traffic from that particular device (such as internet traffic from a MX device), whereas the Clients page might also include internal traffic that does not leave the network (such as inter-VLAN traffic, or locally camera streaming).
Additional Resources
You may also want to review some of the following resources to learn more about the Clients Usage page:

