Configuration Settings Payloads
The Systems Manager > Manage > Settings page allows you to configure the specific settings associated with a particular configuration profile. These settings and profiles can be used to ensure that your devices meet business requirements and receive the configurations your users need to work.
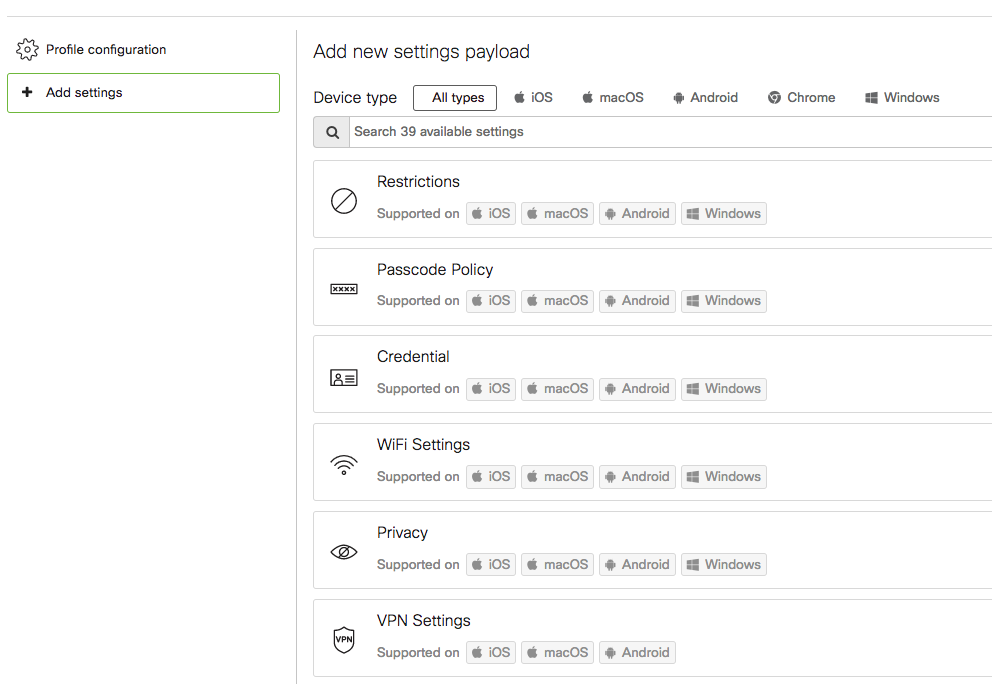
After creating a new profile, click the 'Add settings' option on the left to begin adding settings payloads to your profile. Profiles can contain multiple payloads at once, and multiple profiles can be installed on a device. Your settings and profiles should be tailored to how your device deployment and tag structure are organized.
The rest of this article introduces each of the primary settings payload options.
Cross-Platform Settings
Restrictions
Set various restrictions on managed devices, which allow you to control what access and functionality your end users have. Some examples include blocking iMessage, the App Store, setting a Safari web content filter, enabling single app mode, or Blocking and Allowing iOS apps. Note that some of the iOS restrictions require devices to be supervised to be applied.
For a full list of SM Payload Restrictions broken down per device type, see the restrictions document.
Passcode Policy
Supported on: iOS, macOS, and Android
Enforce passcode requirements when unlocking iOS, Mac, and Android devices. Note that each operating system may enforce each requirement differently, or only support a subset of the configurations displayed. This payload does not allow you to specify a particular password to be pushed down to devices.
If using this in conjunction with the 'Restrictions' payload for iOS, ensure that the 'Allow modification of passcode settings (iOS 9+)' option is selected in restrictions.
Additional information about this setting can be found here.
SCEP Certificate
Supported on: iOS, macOS, tvOS, Android, and Windows
Push SCEP certificates to a device using Meraki's Certificate Authority.
Additional information can be found in the following documentation from Apple.
Certificate
Supported on: iOS, macOS, tvOS, Android, and Windows
Push X.509 (.cer, .p12) certificates to devices. These certificates can be generated by a 3rd party certificate authority or by a locally hosted certificate authority. A good use case for this feature is to push a verified certificate to an iOS device to wirelessly authenticate via 802.1X.
These will automatically populate under the "Trust" feature in a WPA2-Enterprise WiFi profile under the "WiFi" tab. See the "Certificates Payload (Pushing Certificates)" article for more information.
Wi-Fi Settings
Supported on: iOS, macOS, tvOS, Android, and Windows
Push out a wireless profile to your managed devices. Some example use cases for this feature are:
-
Providing an Internet connection for your devices, but do not want to explicitly provide the SSID name or credentials to the end user
-
Pushing out WPA2-Enterprise WiFi profiles with 802.1X authentication (EAP-MSCHAPv2, EAP-TLS, etc.) This can be further configured with "Trusted Certificates" that you upload, utilizing the "Certificate" feature described above.
Additional information can be found in the following documentation from Apple.
Privacy and Lock
Supported on: iOS, macOS, Android, and Windows
Privacy options will allow/prevent Systems Manager from displaying SSID or location information for devices in scope of the profile.
The Lock options control the behavior of the Activation Lock feature on supervised Apple devices. Enabling 'Allow Activation Lock' will allow end users to use Activation Lock in the 'Find My' app with their personal Apple IDs. Enabling 'Allow MDM Activation Lock' will automatically send a command to Apple to enable Activation Lock on a DEP-enrolled device. The command will enable Activation Lock on target devices using the Apple ID of an Apple Business Manager or Apple School Manager administrator.
The "Privacy and Lock" payload setting modifies Dashboard-side configurations, rather than anything local to the device. If you create a profile with only this setting and attempt to push it to a device, the profile will fail to install with an Error: "The Profile is invalid." - In general, this error usually occurs when the profile has no settings configured in the profile.
The best practice for this setting is to nest it inside a profile that has other device settings.
VPN Settings
Supported on: iOS, macOS, Android KNOX, Windows, ChromeOS (L2TP only)
This option allows you to pre-configure client-to-gateway VPN connectivity for your iOS, Android (Knox), Mac and Windows devices with support for multiple connection types. Non-Knox Android devices should use solutions like AnyConnect, or apps that support AppConfig app settings like Pulse VPN.
If you are hosting client VPN through a Cisco Meraki MX in the same organization, you can use the ‘Sentry’ configuration to automatically configure VPN.
Additional information can be found in the following documentation from Apple.
Apple AirPlay
Supported on: iOS and macOS
With AirPlay configuration in Systems Manager, devices can be pre-provisioned with the connection details for AirPlay devices. This can be a great way to secure Apple TV and other AirPlay resources from unauthorized users while ensuring that presenters' devices have all the information required to connect.
Systems Manager can also be customized to only list specific AirPlay devices, allowing for restricted general access to these resources.
Additional information can be found in the following documentation from Apple.
Apple AirPrint
Supported on: iOS and macOS
Systems Manager can remotely deploy AirPrint network printer settings to Apple devices. This allows for seamless printer configuration without the need for a physical connection to the printing device.
Additional information can be found in the following documentation from Apple.
Contacts
Supported on: iOS and macOS
Allows you to sync contacts with a custom server using the CardDAV protocol.
Note: It is best practice to keep this payload in it's own profile. If this payload is in a nested profile, profile updates will force users to manually re-enter their password.
Additional information can be found in the following documentation from Apple.
Encrypted DNS
Supported on: iOS and macOS
Configure Encrypted DNS settings using HTTPS or TLS. When the setting is pushed from the Dashboard it only applies to managed WiFi networks. When installed manually using Apple Configurator, this setting also applies to cellular.
Additional information can be found in the following documentation from Apple.
Managed App Config
Supported on: iOS, tvOS, and Android
Preconfigure specific applications installed on your managed devices via key/value pairs. See the article Managed App Settings for more info.
Exchange ActiveSync Email
Supported on: iOS and Android KNOX
Deploy Microsoft Exchange email configurations to the native Mail app. For more information, see the article Configuring an Exchange ActiveSync Profile for more details.
Additional information can be found in the following documentation from Apple.
Backpack Item
Supported on: iOS and Android
Backpack allows administrators to securely deliver content like student lesson plans or employee resources to managed devices. See the full article here for more info.
Web Clip
Supported on: iOS and macOS
Web clips are shortcuts to web URLs (similar to browser bookmarks) that appear on the homescreen of iOS devices for an easy way to access commonly-visited websites. Please be sure that the icon you upload is less than 144 x 144 pixels and in .png format. See the full article on web clips, as well as additional information found in the following documentation from Apple.
Single App Mode (Kiosk)
Supported on: iOS Supervision and tvOS Supervision
Supervised iOS and tvOS devices can be locked down to display a single application using the Single App Mode payload.
Additional information can be found in the following documentation from Apple.
Apps in single app mode will not be able to update. The app must be able to close in order for the app to update. To close the app it must be either removed from single app mode or a different app must be pinned to single app mode.
Web Content Filter
Supported on: iOS Supervision and macOS 10.15+
On iOS devices, configure content filters for all web requests based on pre-determined categories or admin-defined domains. On MacOS devices, define the settings for a third-party web content filtering app. See the full article Web Content filtering for more info.
Additional information can be found in the following documentation from Apple.
Global HTTP Proxy
Supported on: iOS Supervision, macOS, and tvOS Supervision
Specify a web proxy address to filter all HTTP traffic to and from iOS devices. Devices can only receive one of this type of payload.
Additional information can be found in the following documentation from Apple.
Education Configuration
Supported on: iOS and macOS
Configure Apple School Manager Classroom settings.
In iOS, this payload must be sent over the device channel. Additionally, supervision is required unless the payload only specifies as teacher configuration.
In macOS, this payload must be sent over the user channel. Student payloads are supported in macOS 10.14.4 and later - for more information see the following documentation from Apple.
Notifications
Supported on: iOS Supervision and macOS
Configure notification settings on a per app basis. Requires device supervision.
Additional information can be found in the following documentation from Apple.
Single Sign On Extension
Supported on: iOS 13.0+ and macOS 10.15+
Deploy settings for third-party Single-Sign On apps, including the Apple Enterprise Connect extension. For more information, see the article Extensible Single Sign-on MDM payload settings for Apple devices.
Setup Assistant
Supported on: iOS and macOS
Choose which settings will be skipped when users launch the Setup Assistant on Mac or iOS devices.
Additional information can be found in the following documentation from Apple.
Android Settings
Samsung Knox
Knox-specific settings for Android devices enrolled through Knox and not Android Enterprise. For information on these features, see the Knox article. For more info on different types of Android enrollments, see the Android Enrollment article.
App Permissions
This setting allows for custom application permissions. Examples include denying an application access to the device's contacts, saved payments methods and even network access. Application permissions vary app to app and a list of relevant permissions can be found using the "Fetch permissions" button that appears once an app has been selected.
Device Owner
Requires Device Owner Mode
Contains additional restrictions that can only be applied to Android devices that are provisioned in Device Owner Mode like preventing factory reset or adding additional accounts on corporate-owned assets.
See the section Recommended Android Settings under the Android Enterprise Deployment Guide Article for additional information relating to this setting.
Kiosk Mode
Requires Device Owner Mode
Locks devices into one or multiple selected applications. This can be configured with an unlock code to temporarily exit kiosk mode, or specify application upgrade windows.
See the article Android Kiosk Mode in Systems Manager for more info.
Android Restrictions
This payload includes several System and screen lock restrictions that can be applied to Android devices. Allow/restricts users to access various features like notifications, camera, bluetooth, account modification, and many others.
See the section Recommended Android Settings under the Android Enterprise Deployment Guide Article for additional information relating to this setting.
System Apps
Requires Device Owner Mode
Allows you to block specific pre-installed apps from appearing in device owner mode. Enter in the app identifier, such as 'com.google.android.dialer' for the default Google phone app. Note that different device vendors may have proprietary app IDs. For more information, see this article on Controlling Android System Apps.
Wallpaper & Lock Screen Message
Configure a custom message to be displayed on an Android device’s lock screen, and provide links to images that can be used as the system or lock screen wallpaper.
Always-on VPN
Specify an Always On VPN App to ensure that the data from specified managed apps will always go through a set-up Virtual Private Network. This feature requires deploying a VPN client that supports both Always On and per-app VPN features.
Cross-profile
Configure cross-profile widgets from a set of specified apps to be available in a parent profile.
Google Play Store Settings
Configure the Google Play Store auto-update policy for all apps installed on the device. This configuration does not affect the updating of apps provisioned via custom APK.
Google Play Store App Update Mode
Configure App Auto-Update on a per-app basis in one of the three following modes: High Priority, Default, or Postpone.
When using the High priority mode, the app should update as soon as a new version is published by the developer and has been reviewed by Google Play. If the device is offline at that time, the app will be immediately updated the next time the device is connected to the internet.
When using the Postpone mode, the app is not automatically updated for an initial 90 days after it first became out of date. After this 90-day period, the latest available version of the app is automatically installed using the default update mode. After the app is updated to the latest available version, a new 90-day postponement period will begin from the next time that the developer publishes a new version of the app.
iOS/iPadOS Settings
Calendar
Allow devices to sync corporate calendars (CalDAV) directly to the native Calendar app on iOS.
Additional information can be found in the following documentation from Apple.
Managed Domains
Establish a list of email domains and Safari web domains that will be treated as managed on an iOS device. Emails sent from a managed domain to an external address will be flagged in the Mail app. Downloaded attachments from a managed domain are considered follow the “Managed Open In” rules defined in the Restrictions payload.
On iOS 9.3+, admins may also provide an option to save users’ passwords in Safari from matching URL domains. Multiple password domains can be added.
Additional information can be found in the following documentation from Apple.
Cisco Umbrella
Requires Supervision
Provide complete network visibility and control on supervised iOS devices by leveraging the power of Cisco Umbrella to filter DNS requests against malicious sites. Requires the Cisco Security Connector app. For more information on configuration, see the Cisco Security Connector article.
Cisco Clarity
Requires Supervision
Audit and gain insight into app-level network traffic flows on supervised iOS devices using Cisco AMP. Requires the Cisco Security Connector app. For more information on configuration, see the Cisco Security Connector article.
Wallpaper
Requires Supervision
This payload allows you to specify the background wallpaper and lock screen image for your supervised iOS devices. Choose images with dimensions that exactly match your devices' dimensions.
Additional information can be found in the following documentation from Apple.
Google Account
Allows you to push a Google account to Apple devices. Users will be prompted to enter credentials after the payload is pushed.
Additional information can be found in the following documentation from Apple.
Per App VPN
Configure a VPN connection with AnyConnect or IKEv2. The device will only tunnel traffic when the specified applications are launched.
Additional information can be found in the following documentation from Apple.
Network Usage Rules
Allows you to disable cellular and roaming data for specific managed apps. See this article Cellular Data Management with Systems Manager for more infomation.
Additional information can be found in the following documentation from Apple.
Home Screen Layout
Requires Supervision
Allows you to specify how application icons will be arranged across devices. This prevents users from rearranging icons, or uninstalling apps from the homescreen. Apps can still be removed from Settings > General > Storage & iCloud Usage > Manage Storage . Note that apps that are installed that are not explicitly placed in this payload will appear in random order behind the icons that are set. Requires iOS device supervision. See the full article on configuring HSL.
Additional information can be found in the following documentation from Apple.
Lock Screen Payload
Requires Supervision
Configure a custom message or asset tag information to be displayed on the lock screen for an iOS device. Automatic properties such as Network name, Device name, or Device serial can be used in these fields.
Additional information can be found in the following documentation from Apple.
eSIM Assignment
Allows you to configure an eSIM server URL and the ability to enable the requirement for the device to be network-tethered to run the command.
Additional information can be found in the following documentation from Apple.
Cellular APN Settings (APN)
Allows you to configure both Cellular (default) and Data APNs for iOS devices. The Cellular APN settings require iOS 7 or later. The Data APN settings require iOS 8 or later.
Additional information can be found in the following documentation from Apple.
macOS Settings
System Preferences
Specify which options to lock out on your macOS devices. This payload is compatible on macOS 10.7 to macOS 13.0. It has been deprecated by Apple and is expected to not function on newer releases of macOS. Note that third-party preferences could be limited by pushing a script to install a custom .plist with the software installer. For an example of how scripts can be deployed, see this article Deploying scripts in Systems Manager.
Additional information can be found in the following documentation from Apple.
FileVault
Allows you to enforce FileVault encryption on Mac devices. See this article FileVault, for configuration details.
Additional information can be found in the following documentation from Apple.
FileVault Recovery Key Escrow
Define a specific certificate that can be used to encrypt and decrypt the FileVault recovery key. For configuration steps, refer to the FileVault article.
Additional information can be found in the following documentation from Apple.
App Store
Configure restrictions for accessing the Mac App store. It is supported only on User channel (Apple User profiles).
Additional information can be found in the following documentation from Apple.
Login Window
Specify the login window behavior on a Mac device including disabling or hiding components on the login screen.
Additional information can be found in the following documentation from Apple.
Dock
Specify the dock settings such as dock size, position, or apps that can be added to the dock.
Additional information can be found in the following documentation from Apple.
Firewall
Enforce Firewall settings including preventing unauthorized applications, programs, and services from accepting incoming connections.
Additional information can be found in the following documentation from Apple.
Kernel Extension Policy
Kernel Extension (KEXT) is a macOS feature which allows dynamic loading of code into the Kernel without needing to re-compile them. They are usually implemented as Bundles and this payload lets you to configure the KEXT’s on behalf of an end user.
Additional information can be found in the following documentation from Apple.
Privacy Preferences
Accept or deny permissions for various apps under the ‘Privacy’ tab of the ‘Security & Privacy’ preference pane.
Additional information can be found in the following documentation from Apple.
Associated Domains
Allows you to define domains where an app can be linked to an extensible app SSO, universal links, or password autofill service on a Mac.
Additional information can be found in the following documentation from Apple.
Content Caching
Allows you to modify the settings for the content-caching service on macOS.
Additional information can be found in the following documentation from Apple.
System Extensions
Allows you to extend the capabilities of macOS by installing and managing system extensions in the device user space. You can create a dictionary of approved system extensions, and map the dictionary team identifiers (keys) to arrays of bundle identifiers, where the bundle identifier defines the system extension to install. Additional information can be found in the following documentation from Apple.
Additional information can be found in the following documentation from Apple.
Chrome Settings
Enrollment
Force device to re-enroll into this domain after wiping.
Sign-in
Sign-in options & user account Allow list.
Device updates
Auto update settings including auto checking for updates and auto installing updates.
Kiosk mode
Lock device into one app.
Reporting
Reports the device state and tracking the recent device users.
Miscellaneous Settings
System time zone settings and other various settings.
tvOS Settings
AirPlay Security
Define the password prompt behavior and network connection type for AirPlay connections on an Apple TV.
Conference Room Display
Requires Supervision
This payload forces the Apple TV into Conference Room display mode with an optional message displayed on the screen.
When Conference Room Display mode and Single App mode are both enabled, Conference Room Display mode is active and the user canʼt access the Single App mode App.
Windows
BitLocker
Allows you to enable local disk encryption on Windows 10 and Windows 11 devices using Windows BitLocker.
See the article Windows BitLocker Encryption with Meraki Systems Manager for more info.

